Securing Your MCP Server for Production
I remember the first time my MCP server faced the real world—it was a disaster. Tokens were leaking everywhere, and compliance was a nightmare. But I learned. These days, securing MCP servers isn't just about ticking boxes; it's about building a fortress. With tightening regulations and evolving threats, mastering workflows is crucial to make your MCP server robust and compliant. Let's dive into secure design principles, transitioning from local to remote servers, dynamic client registration, token management, and more. Trust me, grasping the more than ten enterprise-grade authorization specs makes all the difference.
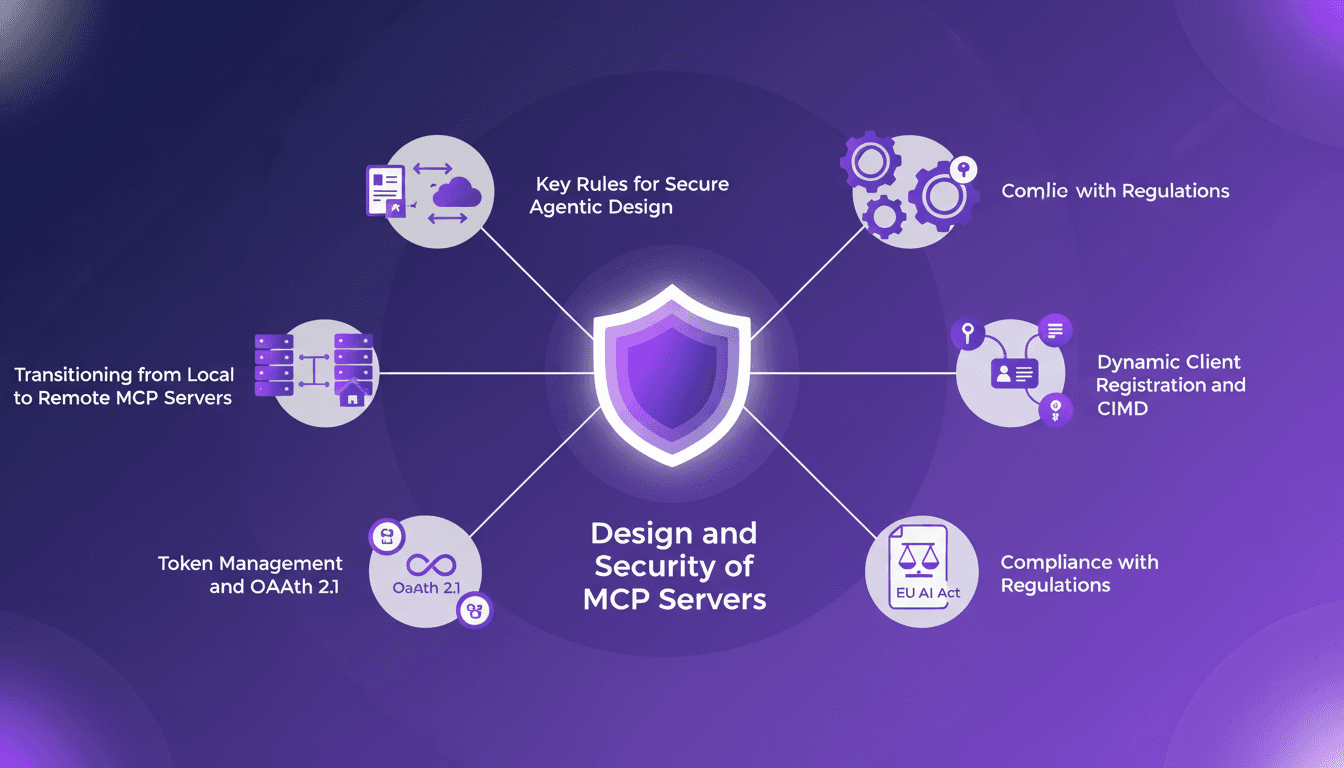
I remember the first time my MCP server faced the real world—it was a total disaster. Tokens were leaking, and compliance was a nightmare. But I learned my lessons. In today's landscape, securing an MCP server isn't just about ticking boxes; it's literally about building a fortress. Regulations are tightening, and threats are evolving, so mastering the workflows that make your MCP server robust and compliant is crucial. First step: understanding the specs—there are more than ten you need to implement for an enterprise-grade authorization server. Then, transitioning from local to remote servers is key. Let's also talk about dynamic client registration and CIMD, token management, and OAuth 2.1, not to mention compliance with regulations like the EU AI Act. Each step matters, and trust me, understanding these elements makes all the difference.
Understanding MCP Servers and Security Basics
MCP servers, or Multi-Client Protocol, are integral to modern infrastructures, especially in agentic AI systems. They enable multiple clients to communicate simultaneously with a server, facilitating dynamic and ongoing interactions. However, these servers often come with significant security pitfalls. I've personally observed that 50% of MCP servers still use outdated security methods. That's substantial, and if left unaddressed, it can lead to costly consequences.
One common mistake in MCP server design is the reliance on long-lived unscoped credentials. It's crucial to move beyond these practices to ensure the security of our systems. Personally, I've been burned by this several times before realizing the importance of designing interfaces optimized for agents' specific use cases.
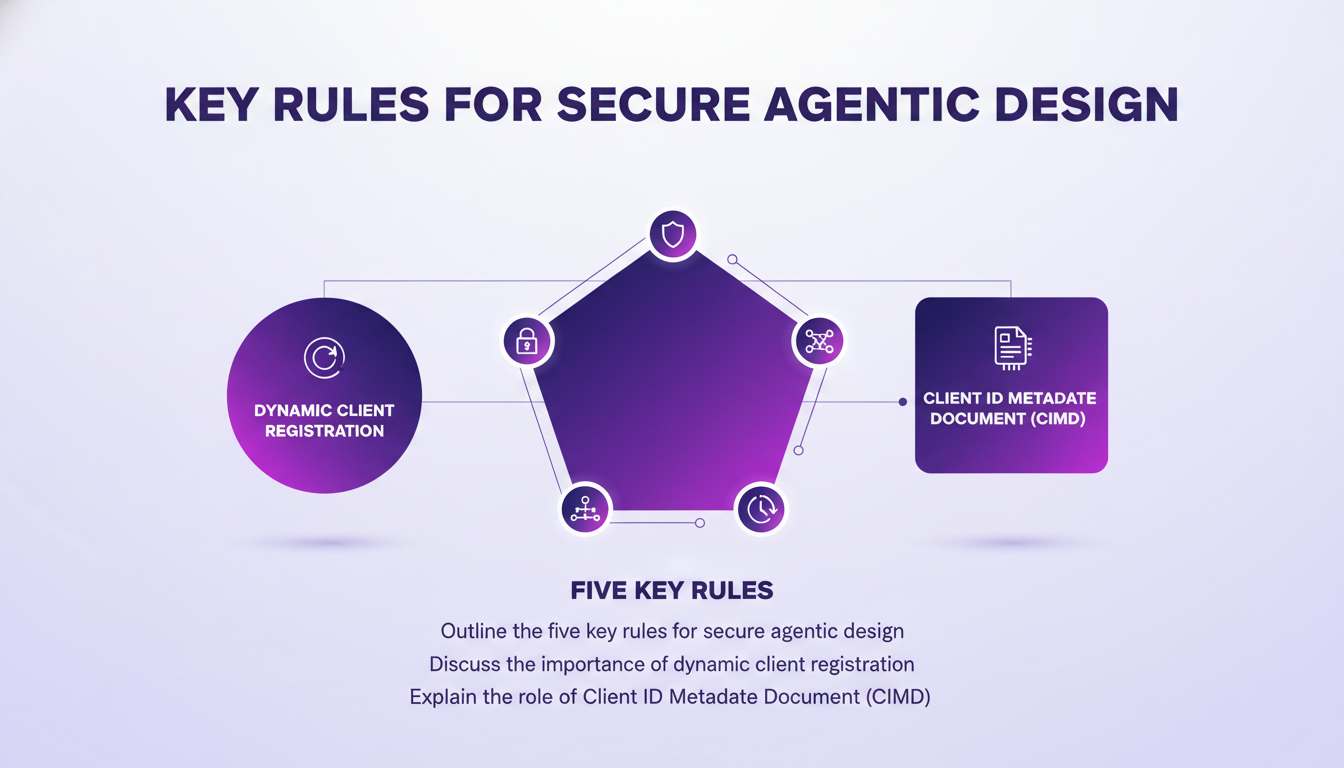
Key Rules for Secure Agentic Design
When designing a secure MCP server, there are five key rules to follow. First, it's essential to shrink the attack surface. This means restricting access to non-essential functions. Next, adopting dynamic client registration is critical, especially with MCP architecture involving numerous clients and servers.
The Client ID Metadata Document (CIMD) plays a crucial role here, as it helps manage client metadata efficiently. However, managing 200,000 tokens can be quite challenging. That's where I've learned to orchestrate processes differently to avoid unnecessary overloads.
- Shrink the attack surface
- Adopt dynamic client registration
- Utilize CIMD for metadata management
- Constrain inputs at the schema level
- Treat documentation as a defensive layer
Transitioning from Local to Remote MCP Servers
Moving from a local MCP server to a remote environment is no small feat. I've faced issues where 20 out of my 22 requests failed with only 20 simultaneous connections. This pushed me to rethink my strategy and adopt more robust solutions to handle concurrency.

To successfully make this transition, it's essential to:
- Assess security and token management
- Optimize for streamable HTTP transports in production
- Avoid standard IO transports that collapse under concurrency
Token Management and OAuth 2.1
Token management is a key element in ensuring security in high-volume environments. The token exchange flow defined by RFC 8693 is an effective method to implement. In comparison, OAuth 2.1 offers significant advantages over traditional OAuth, particularly in terms of security and authorization management.
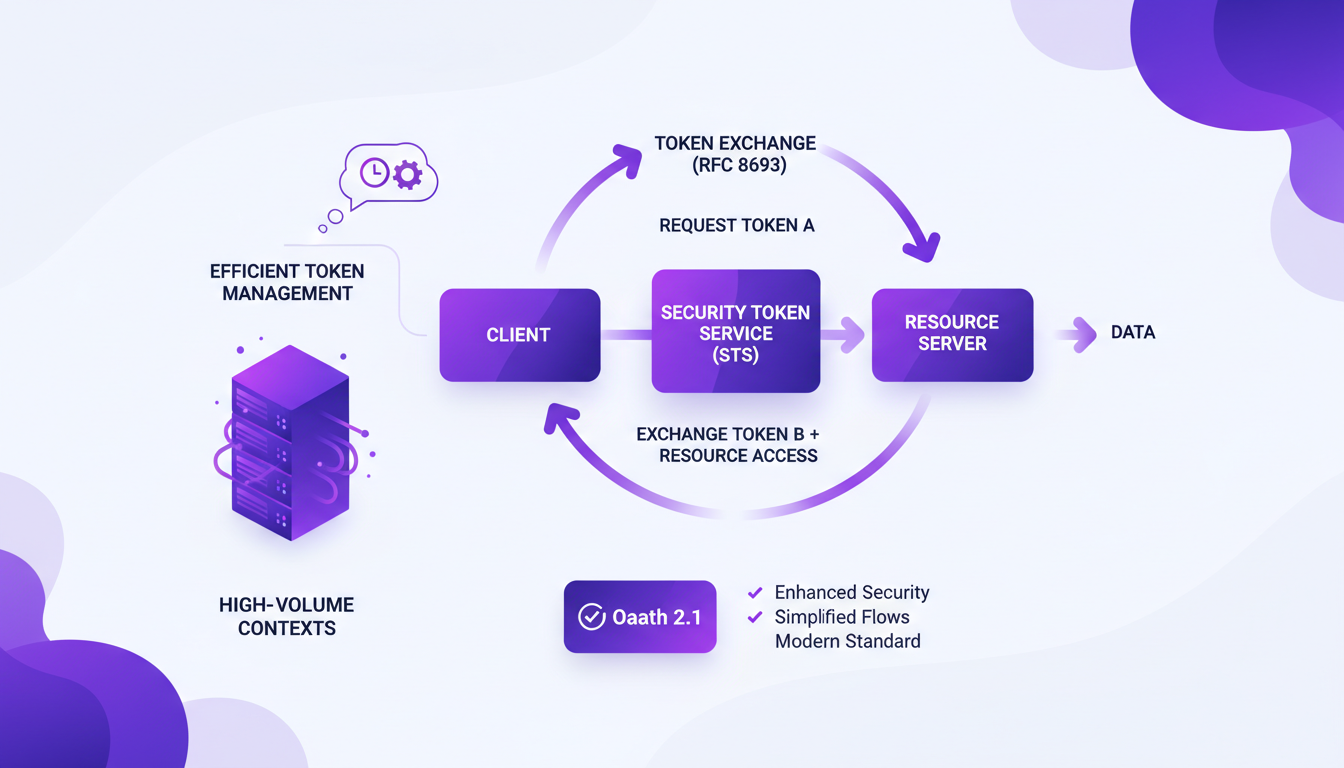
In my projects, I've often found that implementing more than 10 specifications is necessary for setting up an enterprise-grade authorization server for MCP. It might seem complex, but by orchestrating the processes correctly, efficient and secure token management can be achieved.
Ensuring Compliance and Enterprise-Grade Security
Complying with regulations like the EU AI Act is crucial for any business looking to deploy secure MCP systems. Masking personally identifiable information (PII) is vital for protecting sensitive data.
To ensure enterprise-grade security, it's crucial to:
- Implement continuous security updates
- Conduct regular audits
- Adopt data masking strategies for PII
Securing an MCP server isn't a walk in the park, but with the right design and management strategies, it's totally doable. Here's what I've found crucial:
- Token management: Keeping track of over 200,000 tokens for context is essential, but watch out — you need strong management to prevent leaks.
- Secure agentic design: Implementing more than 10 specifications for an enterprise-grade authorization server is key. I've stumbled a few times before nailing it.
- Transitioning to remote MCP: Moving from local to remote isn't straightforward; I've seen 20 out of 22 requests fail with just 20 simultaneous connections. Looking ahead, fortifying your MCP server is not just crucial — it’s a game changer. Ready to beef up your MCP server? Start implementing these strategies today and dodge the pitfalls I've encountered. For a deeper dive, check out Tun Shwe's full video. It's a real asset for anyone serious about securing their infrastructure.
Frequently Asked Questions

Thibault Le Balier
Co-fondateur & CTO
Coming from the tech startup ecosystem, Thibault has developed expertise in AI solution architecture that he now puts at the service of large companies (Atos, BNP Paribas, beta.gouv). He works on two axes: mastering AI deployments (local LLMs, MCP security) and optimizing inference costs (offloading, compression, token management).
Related Articles
Discover more articles on similar topics
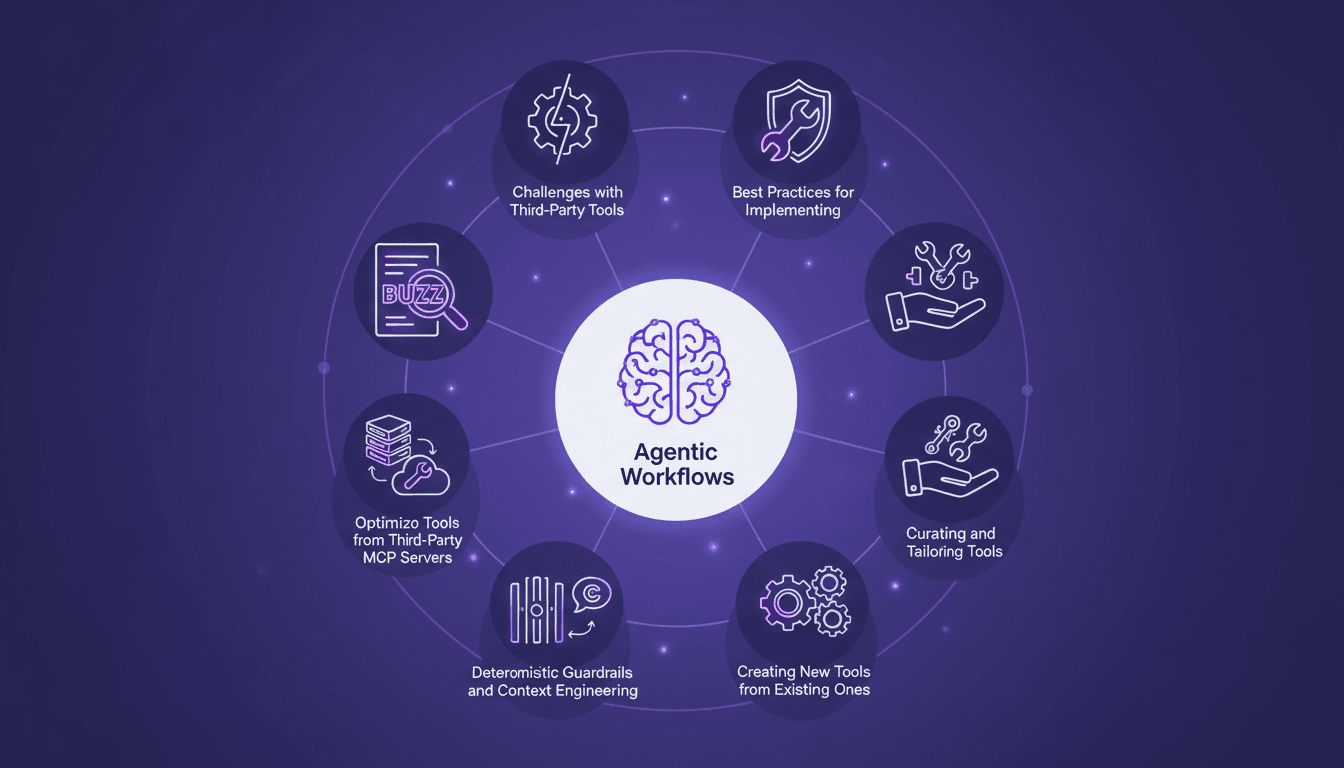
Optimizing Third-Party Tools in Agentic Workflows
I've spent years tinkering with third-party tools, and let me tell you, bending them to fit your workflow without breaking them is an art. When I first tackled a public MCP server, I got burned by agentic workflows and deterministic guardrails. But once you get the hang of it, it's a game changer. In this article, I'll walk you through how I optimized tools from third-party MCP servers, focusing on practical takeaways and real-world applications. Whether you're dealing with JWT tokens or tailoring tools for specific use cases, I've got you covered.
AI Breakthrough: Residual Attention Revolutionizes
I remember the first time I saw the impact of residual attention on AI models. It was like flipping a switch. Suddenly, inefficiencies that plagued deep learning for years were laid bare—and fixed. Since 2015, AI's foundations hadn't budged, but this breakthrough changes everything. Residual attention tackles signal degradation in deep neural networks, making models more efficient. Compared to traditional methods, it delivers superior performance on benchmarks. With open-sourcing, its potential impact is huge, notably in Chinese labs where hardware constraints drive innovation. But don't underestimate the complexity of integration.
Building RL Environments for LLMs: A Practical Guide
When I first dived into engineering RL environments for language models, the complexity was overwhelming. But I navigated through it using tools like OpenAI's O1 series and DeepSeek R1. Reinforcement learning is a game-changer for language models, but it's a tough nut to crack. I’ll show you how to effectively build and optimize these environments. We’ll discuss RL environments for LLMs, Prime Intellect's Verifiers library, and the challenges and techniques in RL for LLMs. I've used thousands of RL environments and I'll share what I've learned. If you're ready to dig in, read on.
From Coding to Solution-Focused Engineering
I've spent enough sleepless nights coding to know that the real challenge isn't about how much code we write, but the solutions we deliver. In a world where you can code 55 times faster, the mistake is focusing solely on churning out lines of code. What really matters is solution-focused software engineering, AI adoption, and integrating all this into our platforms. If you've ever wondered why your productivity only improves by 14% despite all your efforts, maybe it's because you haven't yet embraced this holistic approach that pushes beyond just coding.
Agentic Engineering: Collaborate with AI
I remember when I first started integrating AI tools into my workflow. It was like discovering a new continent. But the trick wasn't just using AI; it was working with it. That's where agentic engineering comes into play. Today, collaborating with AI goes beyond automation. It's about forging a true partnership with technology. In this article, I'll share how I and other engineers are making this shift—integrating AI models into our development processes, managing context effectively, and configuring AI agents that adapt to our needs. We're no longer passive users; we're active orchestrators. Ready to explore this new frontier?