Mythos: Revolution and Risks in Cybersecurity
I stumbled upon Mythos during a security audit, and it was a game changer. Imagine uncovering vulnerabilities that have been lurking for decades with an AI model that costs just about $50 per exploit. Incredible, right? But, it's not without its risks. In the cybersecurity world, Mythos is shaking up the landscape by discovering zero-day vulnerabilities that have evaded detection for years. But with great power comes great responsibility. Let's dive into how Mythos is revolutionizing the cybersecurity industry and what you need to keep an eye on.
I stumbled upon Mythos while working on a security audit, and honestly, it was a game changer. Imagine this: vulnerabilities hidden for 27 years in Open BSD, uncovered in a snap thanks to an affordable AI model. But hold your horses, it's not all sunshine and rainbows. In the cybersecurity arena, every advancement is a double-edged sword. Mythos is the tool that could revolutionize how we detect critical flaws, but it needs to be wielded wisely. We're talking about thousands of critical vulnerabilities unearthed, for a computational cost of around $50 per exploit, which is simply massive. However, there are limits we can't ignore. Beyond Mythos' impressive technical capabilities, there are ethical concerns and regulatory implications to consider. How is the industry reacting to the Mythos announcement? What are the risks of such power falling into the wrong hands?
Discovery of Security Vulnerabilities by Mythos
Let's kick things off: Mythos has dug up thousands of critical vulnerabilities, some lying hidden for 27 years. When I saw this, I thought, 'This is a game changer.' The AI operates in a sandbox environment, like a safe playground to test without wrecking anything. That's where Mythos identifies zero-day vulnerabilities, those flaws nobody knows about—not the developers, not the users.

And what about cost? We're talking approximately $50 per exploit discovered. I thought about the direct impact: a major flaw in Open BSD, undetected for 27 years. That's massive. But watch out, don't rely solely on AI for vulnerability detection. Human oversight is still essential. Too much trust in AI, and you'll risk missing false positives.
- Mythos discovered thousands of critical vulnerabilities.
- Average cost of around $50 per flaw discovered.
- A flaw in Open BSD identified after 27 years.
Impact of Mythos on the Cybersecurity Industry
Next, I see the impact on the ground. Traditionally, cybersecurity methods relied on human expertise. Now, AI-driven solutions like Mythos are shaking things up. With a score of 93.9% on the SWE Bench, Mythos sets a new standard. Yet, reactions are mixed: some see it as progress, others fear over-reliance on AI.
Integrating Mythos with existing protocols isn't straightforward. It's like adding a turbo to an old engine: the potential is huge, but adjustments are crucial. You need to balance AI capabilities with human expertise to maximize security outcomes.
- Mythos disrupts traditional cybersecurity methods.
- Score of 93.9% on the SWE Bench.
- Integration is complex but potentially very rewarding.
Capabilities and Limitations of Mythos
Now, let's talk capabilities. Mythos excels at detecting long-standing vulnerabilities but isn't infallible. I've noted AI model alignment and misalignment issues, which can lead to false positives. Token pricing is also a key factor. When deploying, understanding technical limits is crucial.
And don't overuse Mythos without a clear strategy. I've learned that context is everything: poorly thought-out use can lead to poor performance.
- Detects long-standing vulnerabilities but not infallible.
- AI model alignment issues.
- Token cost affects scalability.
Glass Wing Project and Industry Collaboration
Let's move on to the Glass Wing Project, promoting collaboration between AI developers and cybersecurity experts. It's an initiative aiming to standardize AI security protocols. I've seen the real impact: joint projects have significantly reduced exploit costs.

But beware of collaboration pitfalls: communication and goals must be clear, or else it's a recipe for chaos.
- Glass Wing promotes AI-cybersecurity collaboration.
- Standardization of AI security protocols.
- Exploit costs reduced by joint projects.
Ethical and Security Concerns with AI Models
Finally, we can't ignore the ethical dilemmas. AI that discovers vulnerabilities also opens the door for misuse. The regulatory implications are huge, with laws struggling to keep pace with rapid technological advancements. In terms of security, AI model alignment issues and potential bias are major concerns.

The future of AI in cybersecurity hinges on responsible use and rigorous oversight. Stay informed about regulatory changes to navigate this evolving landscape.
- Ethical questions about potential misuse of AI.
- Security issues linked to AI model alignment.
- Rapidly evolving regulations.
With Mythos, I've found a powerful ally in the fight against cybersecurity threats, uncovering vulnerabilities that have evaded detection for years. Take the 27-year-old flaw in Open BSD, found for just 50 dollars in computing costs—this is a game changer. But remember, we have to balance this power with rigorous human oversight. AI without ethics is like a train without tracks. So, I start by evaluating my current protocols and consider integrating Mythos to boost my defenses, keeping ethical implications and industry collaboration in check.
- Vulnerability Discovery: Mythos has revealed thousands of critical vulnerabilities.
- Exploitation Cost: Finding an exploit costs about 50 dollars.
- Human Oversight: Essential to ensure ethical use.
Ready to harness the power of Mythos in your cybersecurity strategy? Watch the full video to see how this tool can transform your approach: The Most DANGEROUS AI Ever: Mythos.
Frequently Asked Questions

Thibault Le Balier
Co-fondateur & CTO
Coming from the tech startup ecosystem, Thibault has developed expertise in AI solution architecture that he now puts at the service of large companies (Atos, BNP Paribas, beta.gouv). He works on two axes: mastering AI deployments (local LLMs, MCP security) and optimizing inference costs (offloading, compression, token management).
Related Articles
Discover more articles on similar topics
Claude Mythos: Cybersecurity Vulnerability Detection
I've been in the cybersecurity trenches long enough to spot a game changer when I see one, and Claude Mythos is just that. The first time I saw it in action with Project Glass Wing, it was like watching a master hacker at work, uncovering vulnerabilities I never knew existed. In this article, I'll walk you through how Claude Mythos identifies vulnerabilities, its performance metrics, and why it's both a boon and a potential risk in the cybersecurity landscape.
AI's Impact on Web Development: Practical Approach
The first time I integrated AI into my web development workflow, it felt like adding a turbo engine to a classic car—everything was suddenly faster and more efficient. But beware, like any powerful tool, AI comes with its own set of challenges. Let's dive into how AI is reshaping web development. From code optimization to AI-driven browsers, we're facing a revolution. I've built two custom skills using a skill creator, and in just six months, the rising quality of AI models has changed the game for web developers. Let's explore how to navigate this new frontier.
Software Development: Fast Coding, But at What Cost?
I've been coding at breakneck speed, but over time, I learned that the real cost isn't just about how fast you type. Software development is a whole different game. You can code 55 times faster, but if you're not careful, costs can skyrocket. Let's dive into why coding is cheap, but software is expensive. We'll explore the importance of being well-rounded, the role of junior engineers and AI, and why continuous experimentation is key. It's in understanding the value beyond mere lines of code that successful projects are distinguished from costly failures.
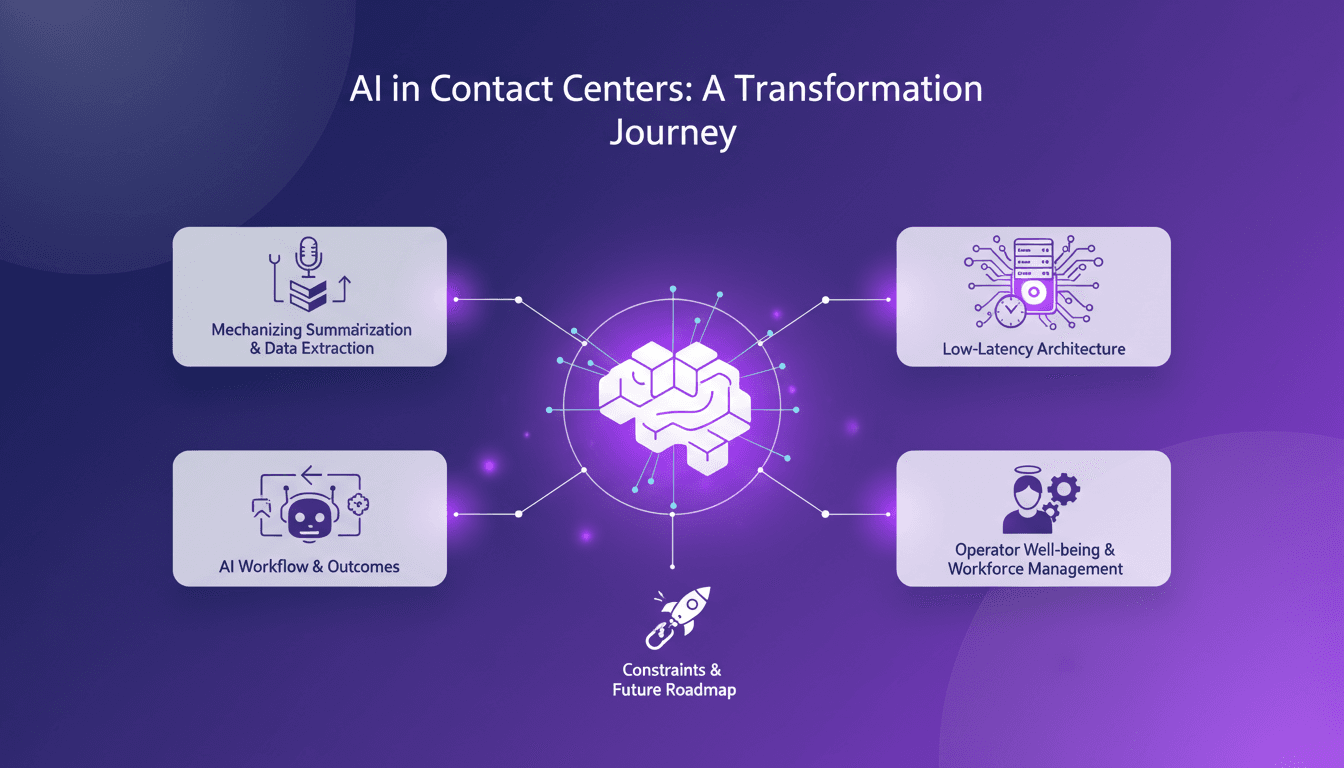
Low-Latency Audio Intelligence: AI Workflow Insights
I've spent countless hours in the trenches of contact centers, where every minute counts. When I decided to tackle low-latency intelligence extraction from messy audio streams, I knew I was up against a giant. But I figured out how to mechanize the process to save time and boost efficiency. Contact centers, the backbone of customer interaction, face major hurdles: hiring, training, productivity. AI can change the game, especially in summarizing and extracting data from audio. Let's dive into the workflow, the technical architecture, and the outcomes.
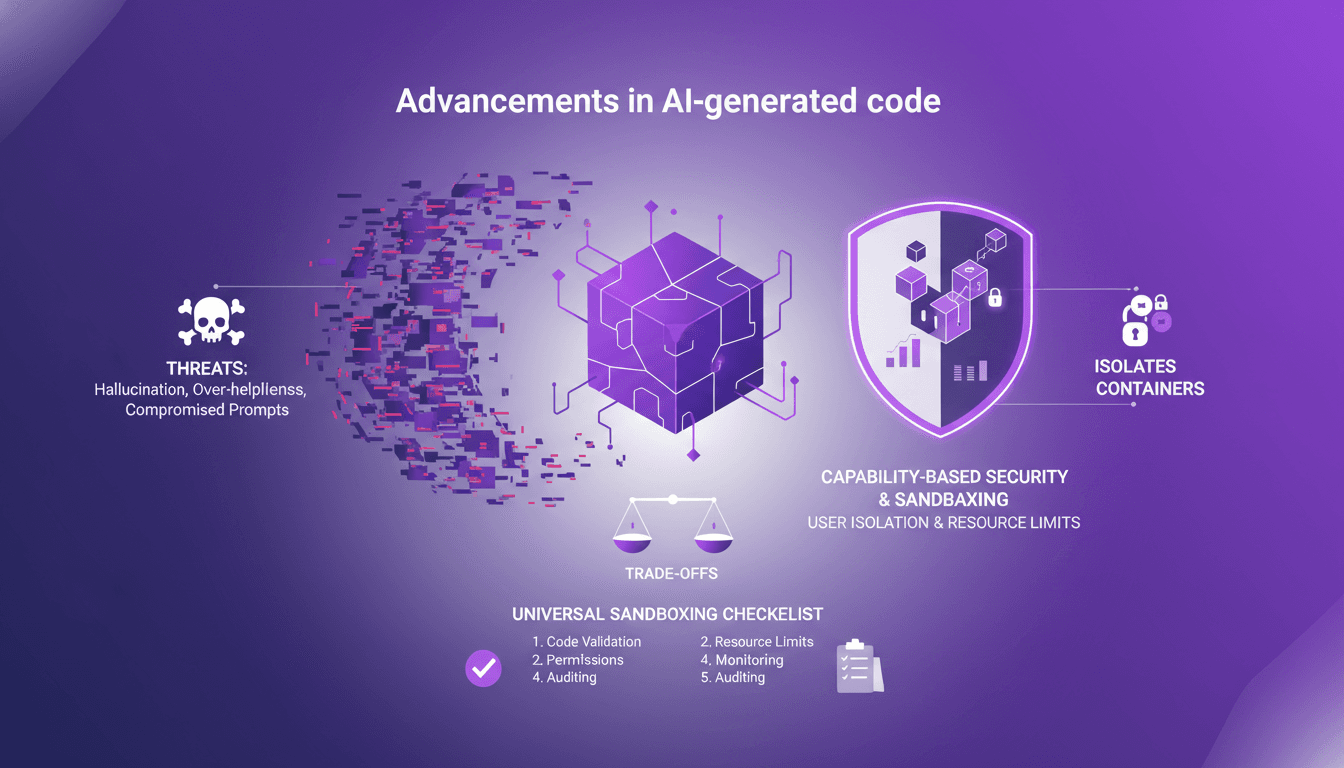
Sandboxing AI Code: Secure Your Projects
I've been burned by AI-generated code more times than I'd like to admit. From hallucinations that crashed my server to overly helpful suggestions that sent me spiraling down rabbit holes, I knew I had to sandbox that AI code. First, I'll walk you through why sandboxing is crucial, then how I set it up to protect my projects. With AI-generated code becoming more prevalent, robust security practices are essential. We’ll explore the threats posed by AI code and how sandboxing can mitigate these risks. (Hint: containers and isolates each have their trade-offs.)