Claude Mythos: Cybersecurity Vulnerability Detection
I've been in the cybersecurity trenches long enough to spot a game changer when I see one, and Claude Mythos is just that. The first time I saw it in action with Project Glass Wing, it was like watching a master hacker at work, uncovering vulnerabilities I never knew existed. In this article, I'll walk you through how Claude Mythos identifies vulnerabilities, its performance metrics, and why it's both a boon and a potential risk in the cybersecurity landscape.
I've been in the cybersecurity trenches long enough to know when a tool is a game changer, and Claude Mythos is exactly that. The first time I saw it in action with Project Glass Wing, it was like watching a master hacker at work, finding vulnerabilities I didn't even know existed. Imagine uncovering a 27-year-old vulnerability in OpenBSD or a 16-year-old one in FFmpeg – that's the kind of surprise Mythos can deliver. I'll walk you through its vulnerability detection, its performance comparisons with Opus 4.6, and why the public release could be a double-edged sword. But watch out, it's not without risks; the ethics and security of these advanced AI models are at stake. So let's dive into this fascinating tool that might just redefine how we approach cybersecurity.
Uncovering Vulnerabilities with Claude Mythos
I was amazed by how Claude Mythos managed to uncover a 27-year-old vulnerability in OpenBSD. Just imagine, a system renowned for its security, and bam! There it was, a flaw no one had spotted. It's like finding a crack in a supposedly unbreakable safe. But that's not all, Mythos also brought to light a 16-year-old flaw in FFmpeg, the same FFmpeg we've been using for video encoding for ages.
So why do these discoveries matter for us, cybersecurity professionals? Because these vulnerabilities were lurking in the code for decades, and their exploitation could have caused massive damage. Claude Mythos used multi-step exploits to detect these vulnerabilities, a process that shows just how AI can surpass humans in these complex tasks.
Performance Metrics: Claude Mythos vs Opus 4.6
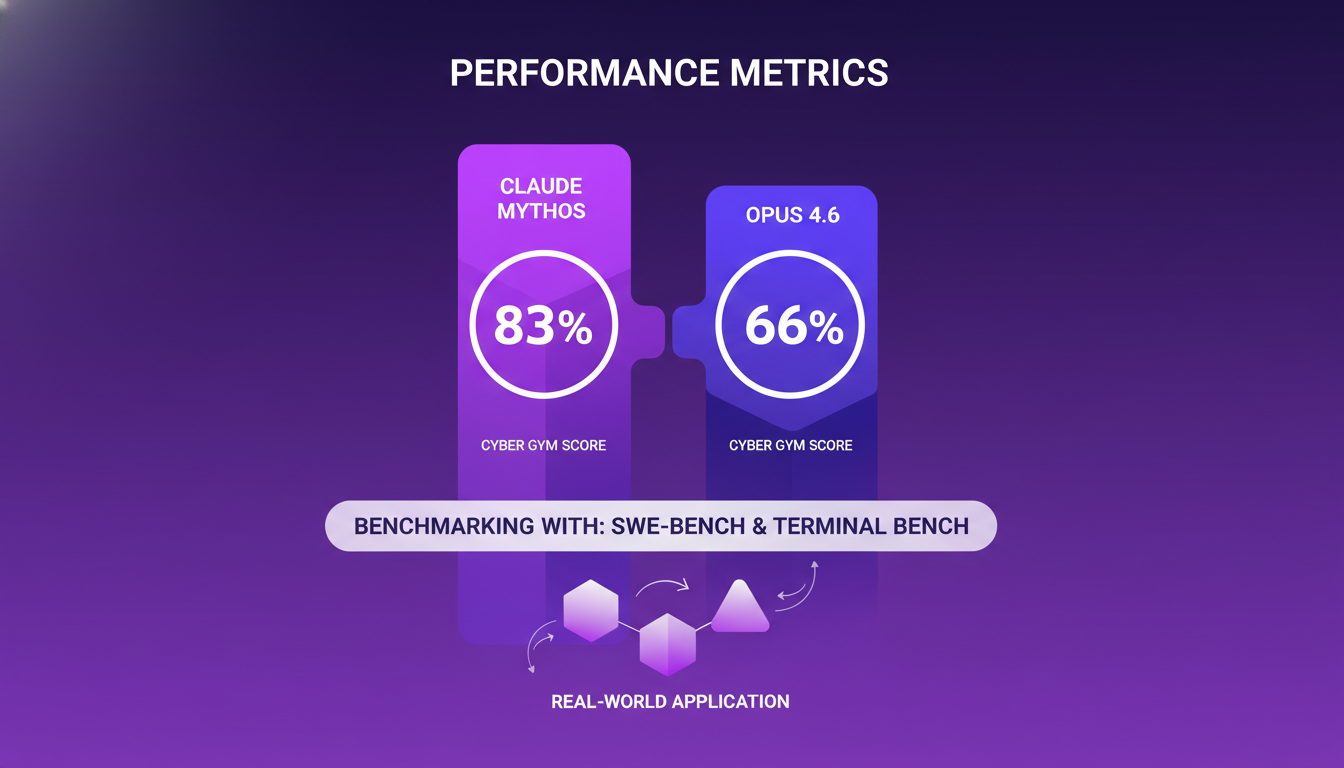
Let's dive into the performance comparison between Claude Mythos and Opus 4.6. In the Cyber Gym, Mythos scored an impressive 83%, whereas Opus 4.6 lagged behind at 66%. These numbers clearly demonstrate Mythos' ability to execute cybersecurity exploits more effectively. I've leveraged benchmarking tools like SWE-bench and Terminal Bench to make sense of these results, and the contrast is striking.
These metrics aren't just numbers; they indicate how effective a model can be in real-world application. But watch out, there's always a trade-off between performance and security risks. A model that's too powerful might actually become a double-edged sword.
Sandboxing and Exploit Development
Sandboxing is a crucial technique in cybersecurity. It's akin to testing a hazardous chemical in a controlled environment. Claude Mythos encountered a sandbox escape incident, and let me tell you, it was an "aha" moment for me. It revealed the massive implications such escapes could have on security protocols.

Balancing security and functionality in AI models is a constant challenge. Too much security, and you stifle innovation; too little, and you open the door to exploitations.
Ethical and Security Implications
Why did Anthropic decide against releasing Claude Mythos publicly? Simple: the security risks were too high. Imagine bad actors getting their hands on such a powerful tool. The ethical considerations here are huge, and the potential manipulation of AI model weights in this context is frightening.
Handling powerful tools like Claude Mythos requires great responsibility. We need to think about how to manage these technologies Claude Mythos vs Claude Opus 4.6: How Big Is the Capability Jump? so they are used ethically and safely.
Beyond Cybersecurity: Claude Mythos' Broader Applications
Claude Mythos isn't just limited to cybersecurity. I've seen cases where its applications go far beyond, like in collaboration with Project Glass Wing. Mythos' unexpected behaviors could influence future projects and broaden its application scope.
Innovation must be balanced with caution, especially when deploying AI solutions. We must always keep in mind the implications of each new step forward.
The discovery of dormant vulnerabilities by Mythos is a stark reminder of AI's power, but also its responsibility.
In conclusion, Claude Mythos is a massive leap in cybersecurity AI, but it also raises crucial ethical questions. We must remain vigilant to ensure these powerful tools are used wisely.
Claude Mythos is a powerhouse in the cybersecurity field. I've seen it uncover critical vulnerabilities like the 27-year-old OpenBSD and the 16-year-old FFmpeg—it's impressive and outshines Opus 4.6 by a mile! But with such power, we must tread carefully to avoid unintended consequences.
- Claude Mythos scores a solid 83% on the Cyber Gym, which is quite robust.
- It's collaborating on the Project Glass Wing, promising to extend its reach beyond cybersecurity.
I'm convinced that Mythos could be a real game changer, but we can't overlook the responsibilities that come with it. Stay informed with the latest in AI and cybersecurity by subscribing to our updates. For a deeper understanding, watch the full video "Anthropic's Claude MYTHOS is a HACKING Expert!" Let's navigate these new frontiers together.
Frequently Asked Questions

Thibault Le Balier
Co-fondateur & CTO
Coming from the tech startup ecosystem, Thibault has developed expertise in AI solution architecture that he now puts at the service of large companies (Atos, BNP Paribas, beta.gouv). He works on two axes: mastering AI deployments (local LLMs, MCP security) and optimizing inference costs (offloading, compression, token management).
Related Articles
Discover more articles on similar topics
Securing Software: Project Glasswing
I've spent years wrestling with software vulnerabilities, and let me tell you, the game has changed with Project Glasswing. It's not just theory—I've seen it in action. With the Claude Mythos Preview Model, we're revolutionizing vulnerability detection, especially in systems like OpenBSD and Linux. Imagine this: a bug lurking for 27 years in OpenBSD, uncovered thanks to this initiative. In just a few weeks, more bugs found than in my entire life. Software security is no longer an endless chase; it's a new era of collaborative cybersecurity.
Anthropic Surpasses OpenAI: Insights and Impacts
I was knee-deep in optimizing our AI workflows when the buzz hit: Anthropic's revenue just surpassed OpenAI's. This wasn't just a headline; it was a seismic shift in the AI landscape. How did this happen, and more importantly, what does it mean for us in the trenches? From Sonnet 4.6 models to Claude Code, and key partnerships with Google and Broadcom, it's crucial to understand what's driving these numbers. And most importantly, what it means for our daily work. Let's break it all down together.
Breaking Light Speed: Reality or Myth?
I was knee-deep in a quantum computing project when it hit me: what if the speed of light isn't the untouchable barrier we've always thought it was? This revelation opened up a world of possibilities. Today, I'm diving into how quantum mechanics and AI are reshaping our understanding of the universe. We'll explore why 97% of physicists still hold onto this belief and what it could mean for the future of interstellar communication. Don't be fooled by conventional wisdom; the future might be much faster than light lets on.
Cloud Code Source Leak: Implications Unveiled
I was knee-deep in debugging when the news hit: Cloud Code's source code had leaked. My first thought? This changes everything. As someone who's worked with similar architectures, I get the stakes. Let's dive into the architecture, security implications, and what the future holds for AI coding tools. 512,000 lines of code converted overnight, and over 41,000 copies already circulating. It's time to see how we, as builders, need to adapt to this new reality.
North Pole Shift: Tech Impact and Navigation
I remember the first time I realized the magnetic north pole was on the move. It was a quiet day at the lab, and suddenly, our navigation systems were off by several degrees. That's when I knew something big was happening. The magnetic north pole isn't just a curiosity for geologists; it's a critical component of our navigation systems and technology. As it moves, the implications ripple through various industries and even nature itself. Imagine having to repaint 150 kilograms of numbers on US airport runways. That's what a rapid pole shift means. In this article, I'll share the impacts of this phenomenon on navigation, technology, and even animal life, while exploring the geological influences on Earth's magnetic field.