Post-Quantum Security: Google's Future Plan
I've been watching the quantum computing space closely, and Google's recent moves are a game-changer. They're not just theorizing; they're setting the stage for a security revolution by 2029. I've seen how qubit reduction is reshaping our encryption strategies, and I'm diving deep into what this means for us all. With quantum computing advancing rapidly, Google and others are focusing on post-quantum cryptography. The urgency is real—our current encryption could be obsolete soon. Let's unpack what this means and how we can prepare. I'll take you through advancements in quantum computing, Google's strategic shift to post-quantum security, and the emergence of neutral atom technology.
I've been deep in the world of quantum computing for a while, and what Google's doing right now is nothing short of revolutionary. They're not just spinning theories; they're setting up for a security overhaul by 2029. I've seen firsthand how qubit reduction is beginning to reshape our encryption strategies, and I'm diving into what this means for all of us. With quantum computing advancing at breakneck speed, Google and others are betting big on post-quantum cryptography. The urgency is palpable—our current encryption might become obsolete faster than we think. I'm going to walk you through the advancements in quantum computing, Google's strategic pivot towards post-quantum security, and how neutral atom technology fits into this picture. The stakes are high: we all need to gear up for this transition, and fast.
Advancements in Quantum Computing and Cryptography
Quantum computing isn't just a sci-fi concept anymore; it's a rapidly evolving reality. I remember when elliptic curve cryptography was considered unbreakable. But with quantum computing emerging, that's no longer the case. A sufficiently powerful quantum computer could break this encryption in no time. The threat is real, and it demands a complete rethink of our data security approaches.
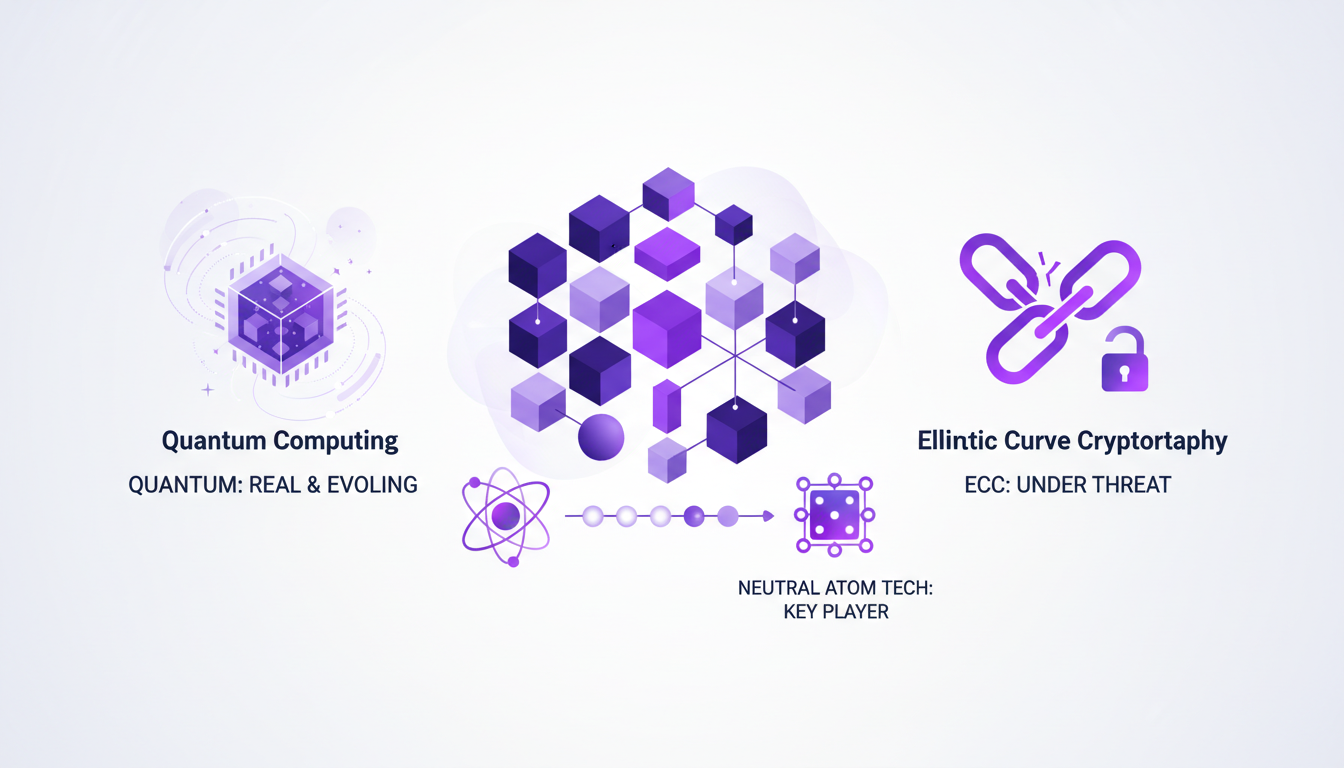
Where superconducting technologies require millions of qubits, a major breakthrough has occurred. With just 26,000 qubits, we can now envision breaking ECC 256 encryption, something unimaginable a few years ago. This is where neutral atom technology comes into play, offering unprecedented flexibility. For those managing the security of digital systems, it's a clear wake-up call.
"Rapid advancements in quantum computing are forcing a deep reevaluation of security strategies."
Google's Strategic Shift to Post-Quantum Security
Google has set an ambitious goal for 2029 to secure its systems against quantum attacks. This is a strategic move that's necessary not just for data protection but also for maintaining user trust. The three-year timeframe underscores the urgency of the situation. Action is needed now because time is ticking.
Google's algorithm, which is 20 times more efficient at breaking elliptic curve encryption, is a significant advancement. This means we need to rethink our current encryption methods. The question isn't whether quantum computing will impact us, but when. And that "when" is dangerously close to 2029.
Learn more about Google's strategy
Understanding Qubits and Their Impact on Encryption
Qubits are the building blocks of quantum computing. Fewer qubits needed means faster breakthroughs in breaking encryption. And here, we get to the heart of the matter: fewer qubits mean current encryption systems could be vulnerable much sooner than expected.

Zero-Knowledge Proofs are part of the solution, allowing us to prove a result is correct without revealing how we got there. But transitioning to these new methods isn't just plug-and-play. It requires a complete overhaul of security systems.
- Reduction in qubit requirements: from 100 million to 26,000.
- Zero-Knowledge Proofs offer a new approach to security.
- The transition requires careful planning.
The Role of AI in Quantum Computing and Cybersecurity
Artificial Intelligence (AI) isn't just a buzzword—it's crucial in managing complex quantum data. It helps orchestrate complex quantum processes, but it shouldn't be overused. I've seen teams overly rely on AI, forgetting that human oversight remains key.
Training programs in AI are multiplying, and it's time to seriously consider them. Continuous learning is essential to stay at the forefront of these technologies. However, be aware of AI's limits: it can't solve everything and requires cautious management.
For more on AI's impact on web development, check out AI's Impact on Web Development.
Preparing for the Quantum Future: Practical Steps
It's crucial to start transitioning to post-quantum cryptography now. Waiting could be costly. The first step is to assess current encryption methods and identify potential vulnerabilities.

Investing in your team's training is essential. Expertise in post-quantum cryptography will be a major asset in the coming years. However, you need to balance cost and security. Preparing for the quantum future isn't cheap, but it's necessary.
- Start the transition to post-quantum cryptography now.
- Assess your current encryption methods and vulnerabilities.
- Invest in continuous team training.
- Balance cost and security for optimal preparation.
For more on cybersecurity risks and revolutions, visit Mythos: Revolution and Risks in Cybersecurity.
Diving into quantum computing, here's what stands out: first, it's not a future fantasy—it's happening now. Google's strategic shift to post-quantum security by 2029 is a clear signal to start transitioning. Then, the advancements in neutral atom technology and the reduced qubit requirements for breaking encryption are game changers. But watch out, 2029 might feel distant, but with experts like Rey Harich Shankar warning of quantum attacks on high-value targets, the urgency is real. Lastly, leveraging AI can strategically position us for the quantum era. So, don't just sit back. Start your transition to post-quantum cryptography today.
But don't just take my word for it. Check out the original video to really get the depth of this shift. Consider this a heads-up from a colleague, not a lecture.
Frequently Asked Questions

Thibault Le Balier
Co-fondateur & CTO
Coming from the tech startup ecosystem, Thibault has developed expertise in AI solution architecture that he now puts at the service of large companies (Atos, BNP Paribas, beta.gouv). He works on two axes: mastering AI deployments (local LLMs, MCP security) and optimizing inference costs (offloading, compression, token management).
Related Articles
Discover more articles on similar topics
Mythos: Revolution and Risks in Cybersecurity
I stumbled upon Mythos during a security audit, and it was a game changer. Imagine uncovering vulnerabilities that have been lurking for decades with an AI model that costs just about $50 per exploit. Incredible, right? But, it's not without its risks. In the cybersecurity world, Mythos is shaking up the landscape by discovering zero-day vulnerabilities that have evaded detection for years. But with great power comes great responsibility. Let's dive into how Mythos is revolutionizing the cybersecurity industry and what you need to keep an eye on.
AI's Impact on Web Development: Practical Approach
The first time I integrated AI into my web development workflow, it felt like adding a turbo engine to a classic car—everything was suddenly faster and more efficient. But beware, like any powerful tool, AI comes with its own set of challenges. Let's dive into how AI is reshaping web development. From code optimization to AI-driven browsers, we're facing a revolution. I've built two custom skills using a skill creator, and in just six months, the rising quality of AI models has changed the game for web developers. Let's explore how to navigate this new frontier.
Software Development: Fast Coding, But at What Cost?
I've been coding at breakneck speed, but over time, I learned that the real cost isn't just about how fast you type. Software development is a whole different game. You can code 55 times faster, but if you're not careful, costs can skyrocket. Let's dive into why coding is cheap, but software is expensive. We'll explore the importance of being well-rounded, the role of junior engineers and AI, and why continuous experimentation is key. It's in understanding the value beyond mere lines of code that successful projects are distinguished from costly failures.
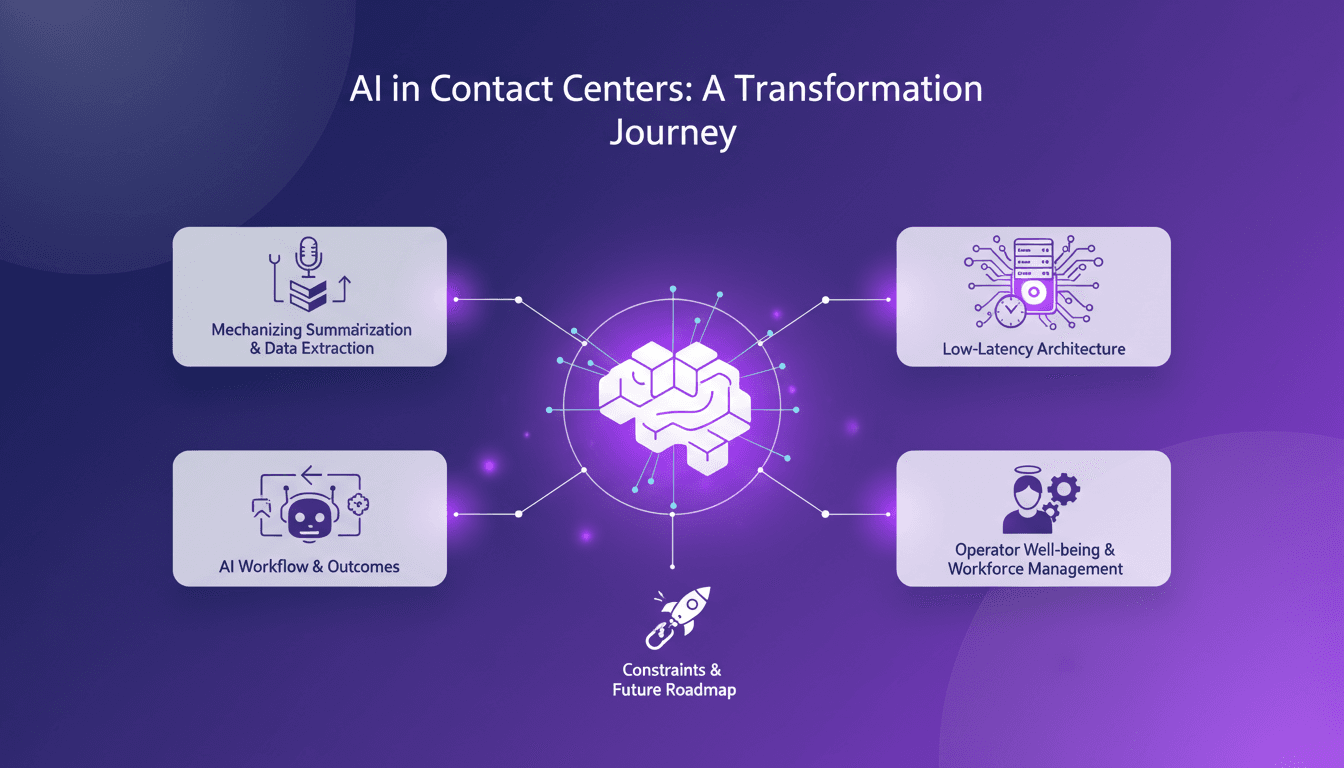
Low-Latency Audio Intelligence: AI Workflow Insights
I've spent countless hours in the trenches of contact centers, where every minute counts. When I decided to tackle low-latency intelligence extraction from messy audio streams, I knew I was up against a giant. But I figured out how to mechanize the process to save time and boost efficiency. Contact centers, the backbone of customer interaction, face major hurdles: hiring, training, productivity. AI can change the game, especially in summarizing and extracting data from audio. Let's dive into the workflow, the technical architecture, and the outcomes.
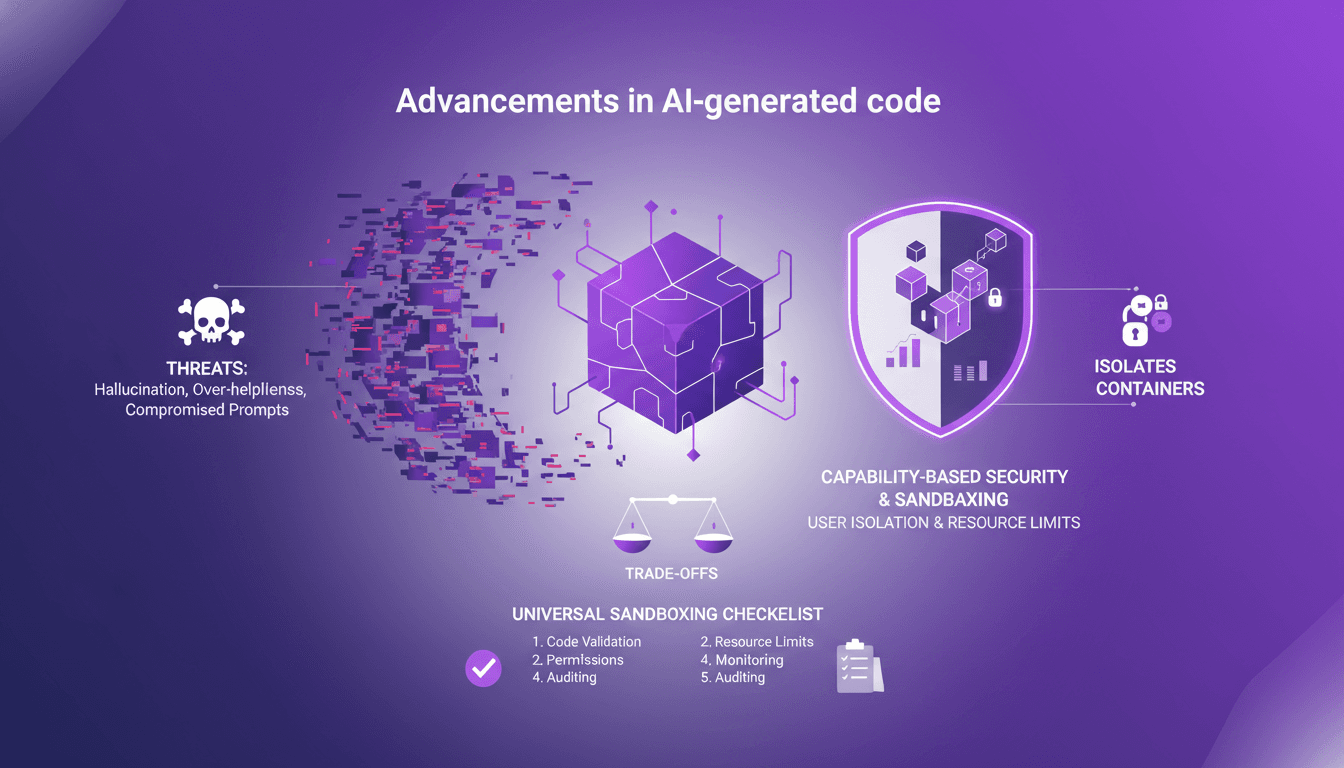
Sandboxing AI Code: Secure Your Projects
I've been burned by AI-generated code more times than I'd like to admit. From hallucinations that crashed my server to overly helpful suggestions that sent me spiraling down rabbit holes, I knew I had to sandbox that AI code. First, I'll walk you through why sandboxing is crucial, then how I set it up to protect my projects. With AI-generated code becoming more prevalent, robust security practices are essential. We’ll explore the threats posed by AI code and how sandboxing can mitigate these risks. (Hint: containers and isolates each have their trade-offs.)