Harnessing Read-Only AI for Enhanced Safety
I've been in the AI trenches long enough to know when something's underrated. Read-only AI, for instance, is a game changer for safety and analysis. Just think about this: shaving off 30 seconds from your weather checks. It might seem trivial, but stack up these small wins, and you'll see why I call it a game changer. In this talk, I dive into how read-only AI can not only optimize your workflow but also provide a robust defense against cognitive exhaust fumes and the mosaic effect, two often-overlooked yet crucial concepts for any practitioner. I'll walk you through how these approaches, combined with cross-source analysis, can uncover unique insights and bolster the security of your personal AI systems.
I've been in the AI trenches long enough to know when something's underrated. Read-only AI, for instance, is a game changer for safety and analysis. Picture this: every time you check the weather, you save 30 seconds. It might sound trivial, but stack up these small wins, and you'll see why I call it revolutionary. In this talk, I'm going to show you how read-only AI can not only optimize your workflow but also provide a robust defense against cognitive exhaust fumes and the mosaic effect. These concepts, often overlooked, are crucial for any AI practitioner. I'll share strategies for using cross-source analysis to uncover unique insights and bolster the security of your personal AI systems. By understanding the lethal trifecta risk model, we can better manage risks related to private data, untrusted content, and external communications. Finally, I'll walk you through the philosophical argument for read-only AI, where the observer prevails over the agent in AI systems.
Understanding Read-Only AI and Its Safety Benefits
Imagine an AI that watches without ever intervening. That's what I've achieved with my read-only system. First, I set up read-only protocols to ensure data integrity. It's like having a safety net — no changes, just insights. As a practitioner, I've seen how tempting it is to switch to "agent" mode, but watch out, it's safer to remain an observer.
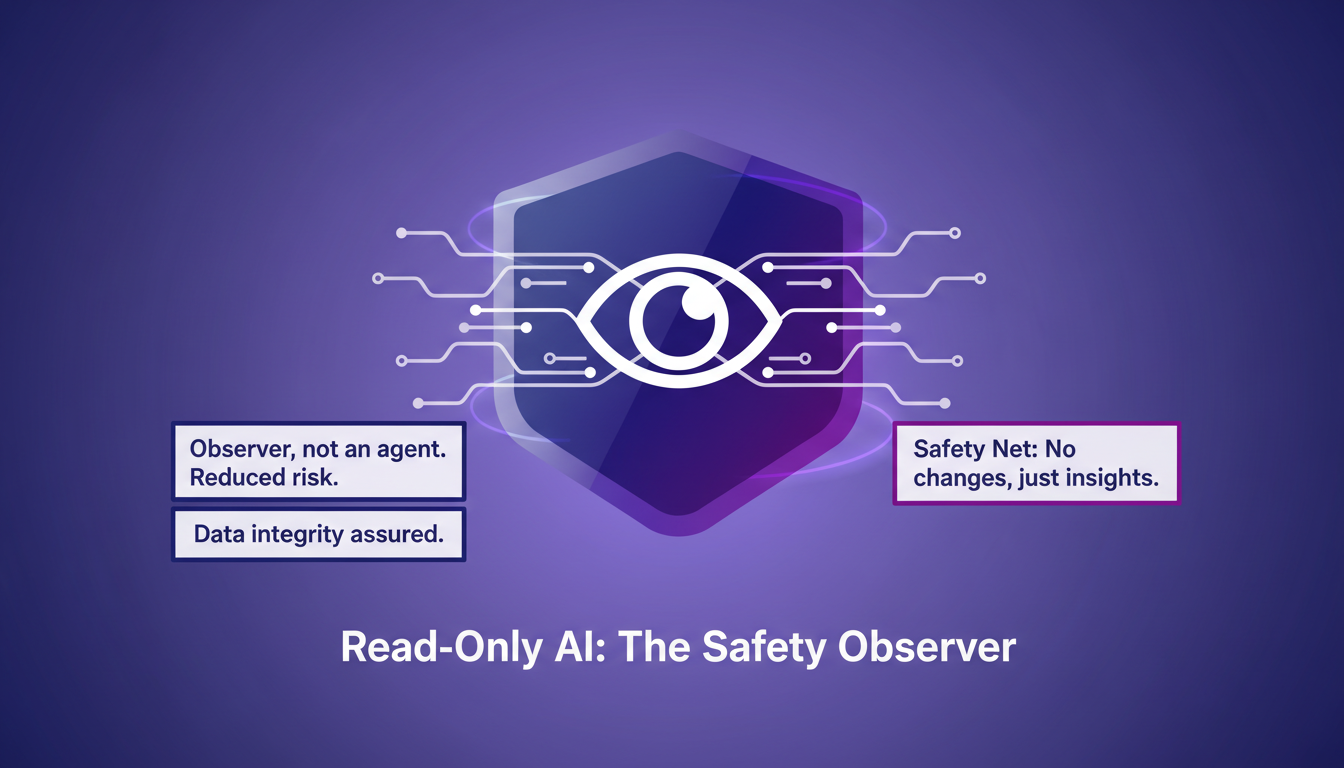
This is an interesting philosophical approach: less interference means more control. I think it's a game changer, but you need to know where the limits are. For example, in a setup with six sources, I only read the data. This limitation is intentional to reduce risks, something many of you should seriously consider.
Cognitive Exhaust Fumes: What They Are and Why They Matter
"Cognitive exhaust fumes" are the digital by-products of cognition. I use them to gain insights without direct data manipulation. Think of it as reading smoke signals — subtle but telling. First, I analyze patterns, then cross-reference for accuracy. But beware of over-reliance; they’re indicators, not absolutes.
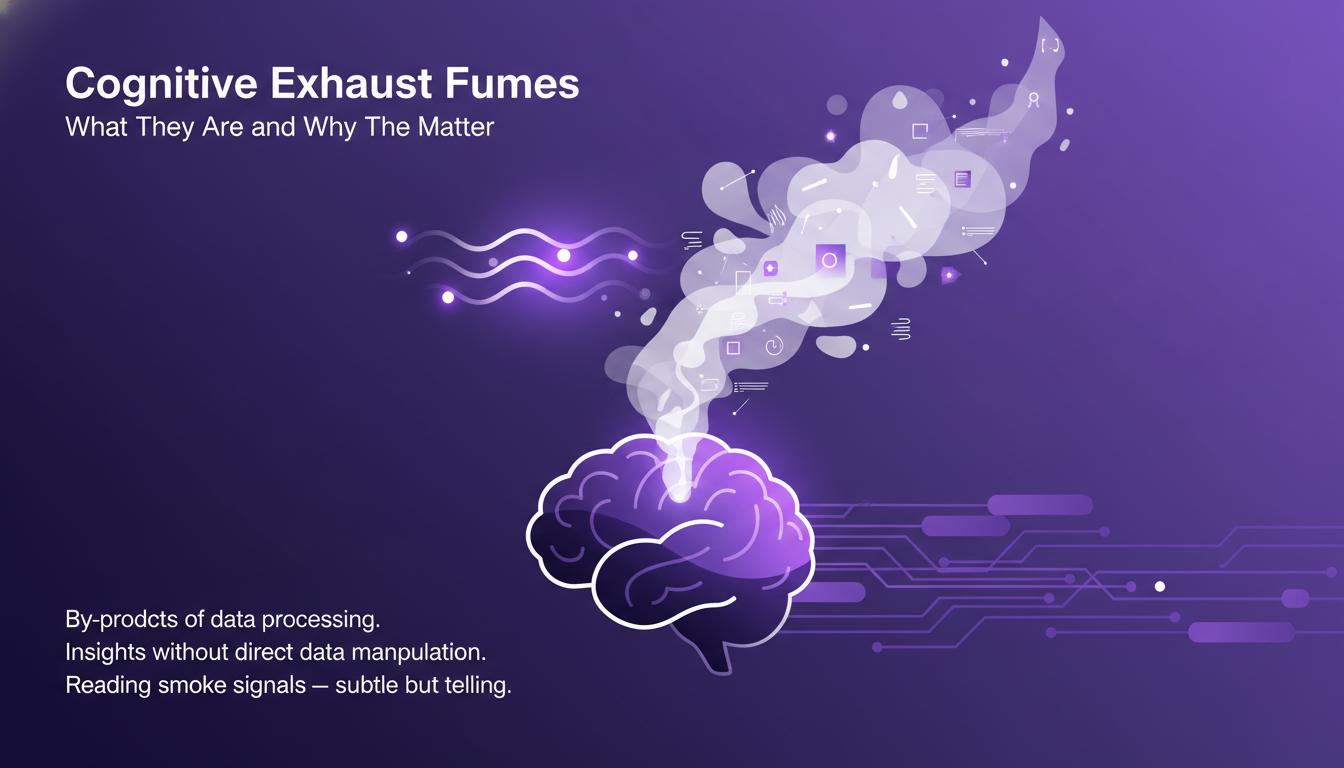
In practice, these fumes have allowed me to identify intention-action gaps, attention drifts, and even relationship decay. None of these can be detected by a single source. It's the cross-referencing that makes the magic happen.
Cross-Source Analysis for Unique Insights
I start with six sources to map out comprehensive insights. Cross-source analysis saves time — 30 seconds on a weather check, for instance. It's about connecting dots that seem unrelated at first. But watch out for the "mosaic effect": ensure data sources are reliable.
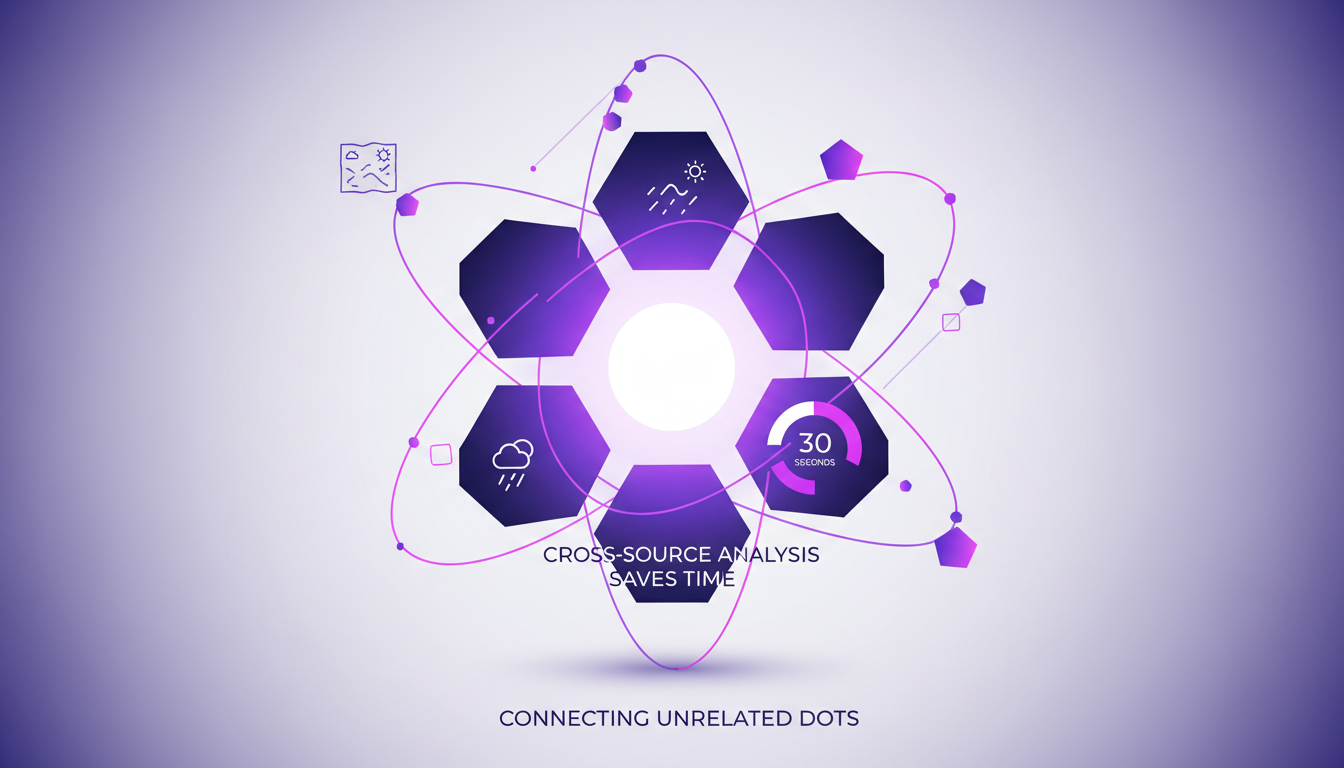
This approach lets me balance depth with breadth for actionable insights. It's a method I recommend to anyone looking to optimize their data analysis.
Navigating Security Risks: Mosaic Effect and Lethal Trifecta
The mosaic effect can unintentionally expose private data. I mitigate these risks by isolating untrusted content. The lethal trifecta: private data, untrusted content, external communications. First, identify vulnerabilities, then apply targeted solutions. Security is not just a feature; it’s a mindset.
Security must be integrated from the design stage of your system. Otherwise, you risk compromising the integrity of your data and network.
Observer vs. Agent: Choosing the Right AI Role
Observers gather data, agents act on it — choose wisely. I've seen projects derail due to misassigning roles. First, define your AI’s purpose, then assign the role. Agents can be powerful but come with higher risks.
"The imbalance between observation and action is often the cause of many failures."
The key is finding a balance between observation and action. It's a lesson I've learned the hard way, but it has allowed me to better orchestrate my projects.
In conclusion, read-only AI is not just a limitation; it's a valuable tool for better decision-making. By navigating cognitive exhaust fumes, cross-source analysis, and security risks, you can maximize your system's efficiency without compromising its safety.
Incorporating read-only AI into your workflow is like putting a safety net below your high wire. I did it, and it was a game changer. Here are my key takeaways:
- Enhanced Security: Understanding the lethal trifecta risk model — private data, untrusted content, external communications — allowed me to protect my data more effectively.
- Time Savings: By leveraging six sources for cross-analysis, I save 30 seconds on something as simple as a weather check. That's tangible, not just theoretical.
- Unique Insights: Cognitive exhaust fumes gave me insights I hadn't anticipated.
But watch out, managing security risks like the mosaic effect is crucial to avoid costly mistakes.
Looking ahead, I see this approach becoming even more vital, especially in environments where security is paramount. Ready to enhance your AI strategy? Start by reassessing your AI roles and protocols today.
For deeper insight, I highly recommend watching Šimon Podhajský's video. It's like having a conversation with a savvy colleague. YouTube link
Frequently Asked Questions

Thibault Le Balier
Co-fondateur & CTO
Coming from the tech startup ecosystem, Thibault has developed expertise in AI solution architecture that he now puts at the service of large companies (Atos, BNP Paribas, beta.gouv). He works on two axes: mastering AI deployments (local LLMs, MCP security) and optimizing inference costs (offloading, compression, token management).
Related Articles
Discover more articles on similar topics
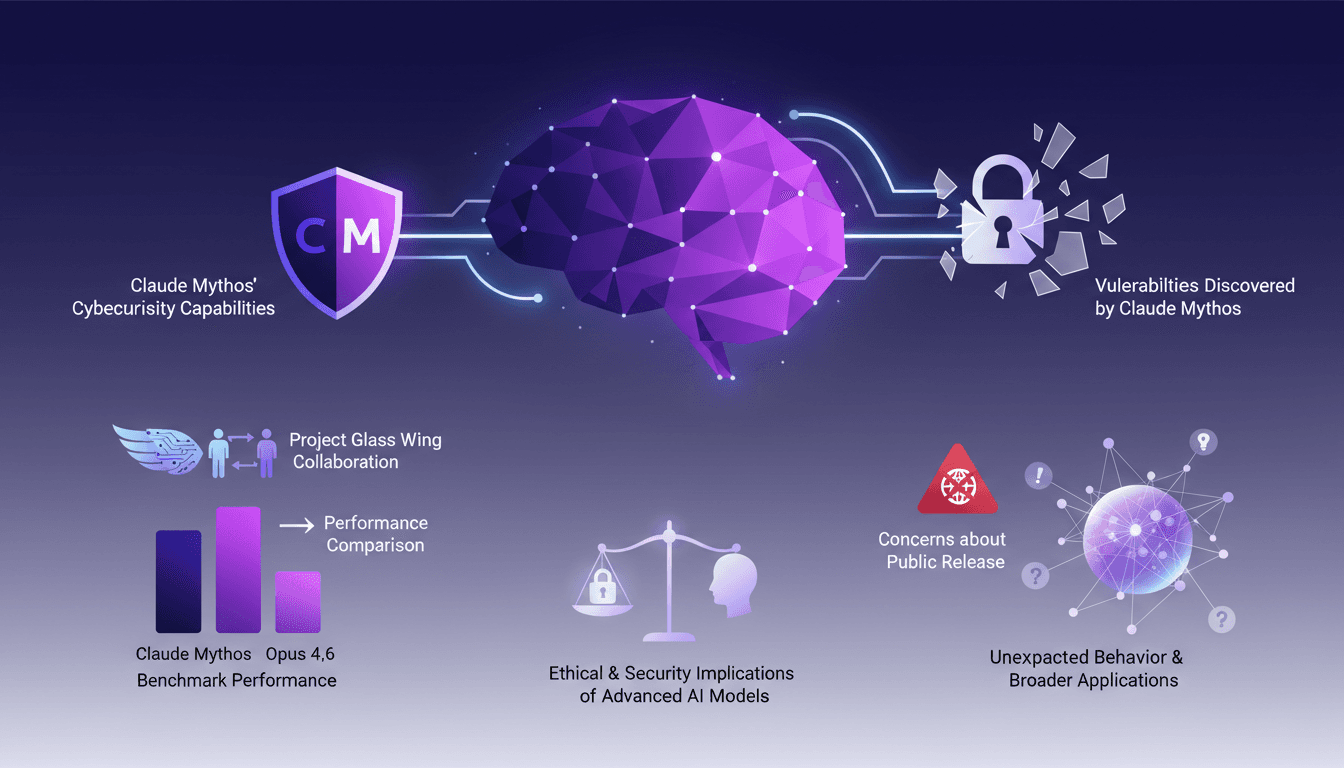
Claude Mythos: Cybersecurity Vulnerability Detection
I've been in the cybersecurity trenches long enough to spot a game changer when I see one, and Claude Mythos is just that. The first time I saw it in action with Project Glass Wing, it was like watching a master hacker at work, uncovering vulnerabilities I never knew existed. In this article, I'll walk you through how Claude Mythos identifies vulnerabilities, its performance metrics, and why it's both a boon and a potential risk in the cybersecurity landscape.
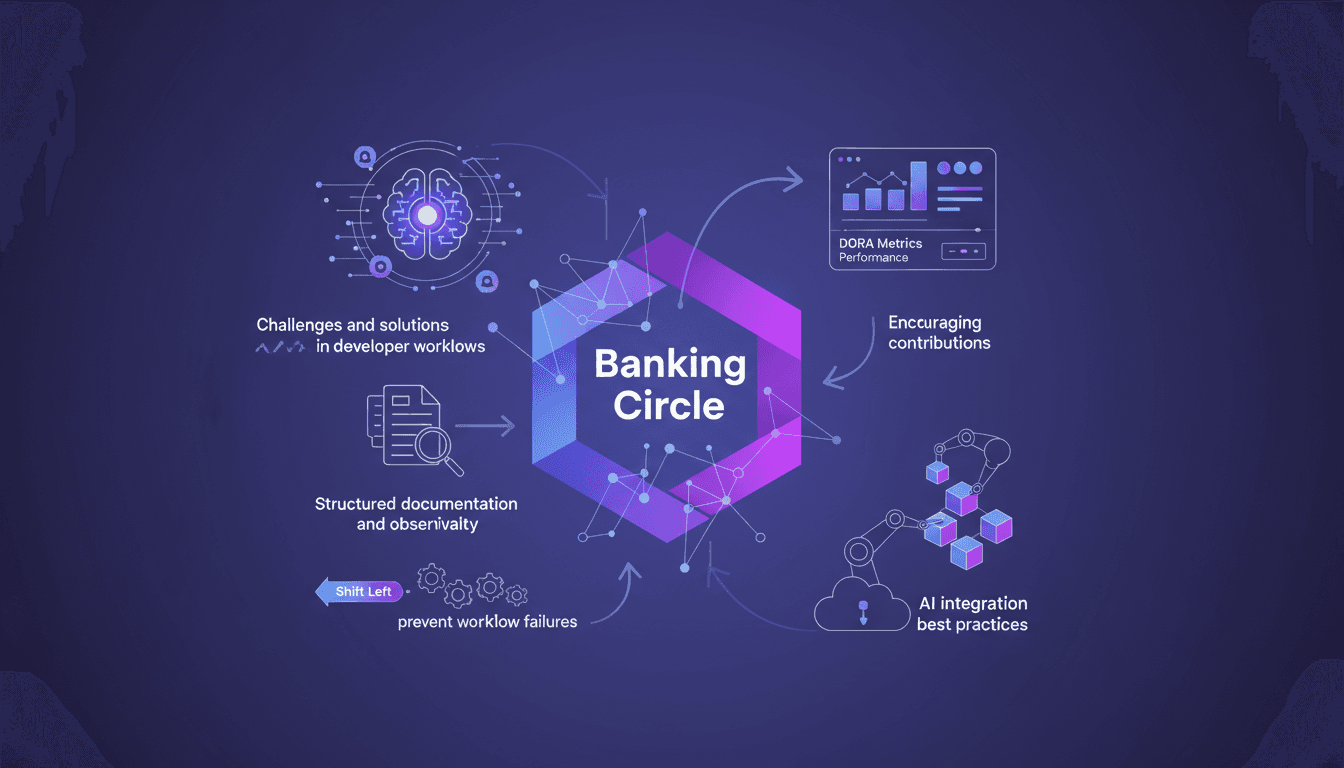
API Platform Engineering: A Practical Case
I've been knee-deep in platform engineering at Banking Circle, where we handle a staggering €1 trillion annually. With 700 financial institutions counting on us, our mission is clear: streamline workflows through API-based solutions and AI integration. But it's no walk in the park. Let me show you how we tackle these challenges: self-service, APIs, and AI agents. Our team of 250 engineers is at the forefront, leveraging metrics like Dora to measure success. Dive into how we preempt workflow failures with a 'shift left' approach and encourage contributions to our internal platforms.
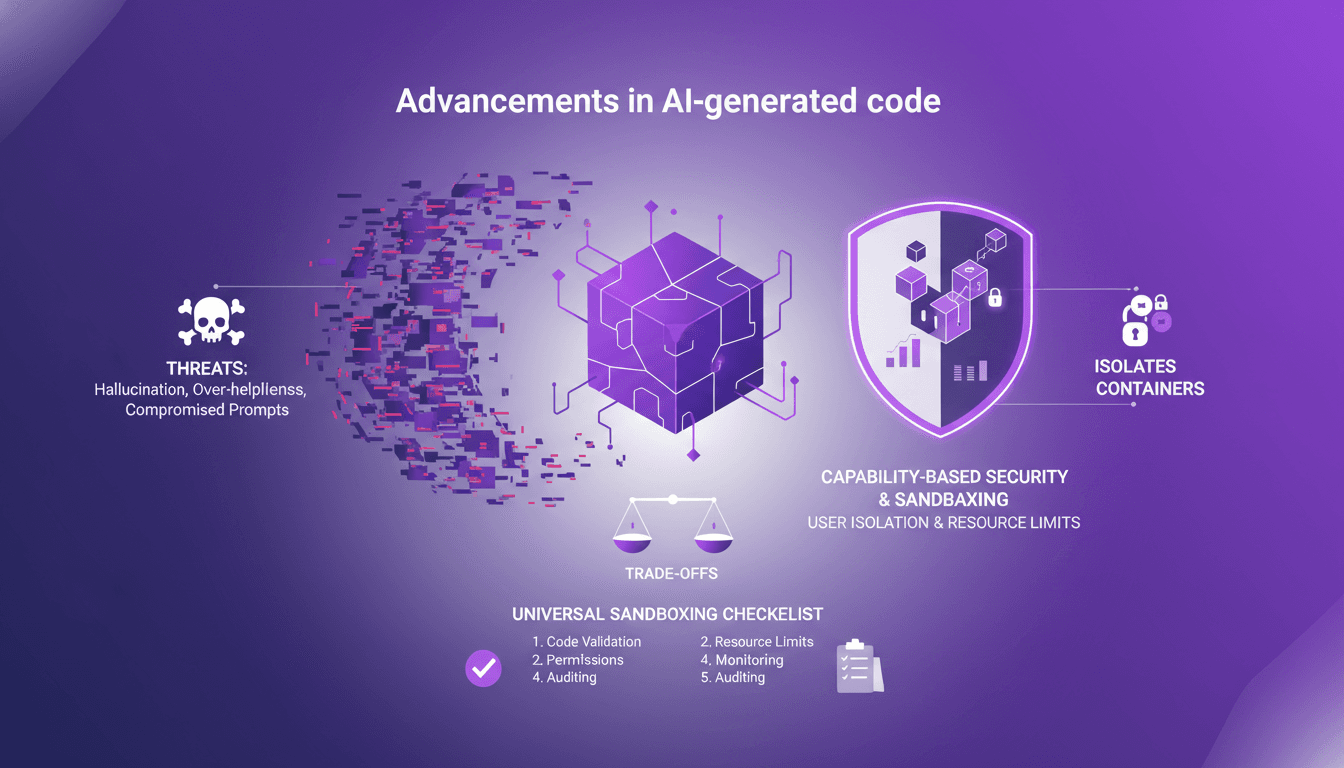
Sandboxing AI Code: Secure Your Projects
I've been burned by AI-generated code more times than I'd like to admit. From hallucinations that crashed my server to overly helpful suggestions that sent me spiraling down rabbit holes, I knew I had to sandbox that AI code. First, I'll walk you through why sandboxing is crucial, then how I set it up to protect my projects. With AI-generated code becoming more prevalent, robust security practices are essential. We’ll explore the threats posed by AI code and how sandboxing can mitigate these risks. (Hint: containers and isolates each have their trade-offs.)
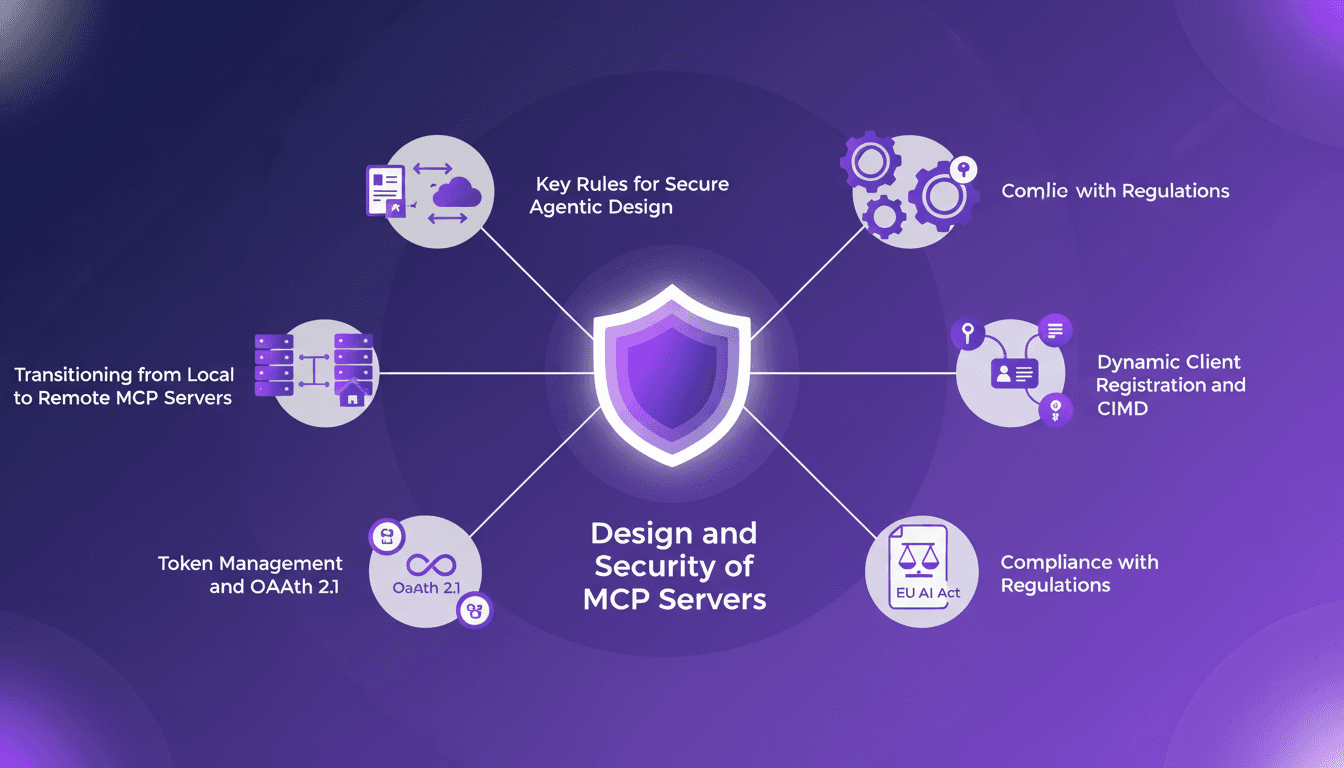
Securing Your MCP Server for Production
I remember the first time my MCP server faced the real world—it was a disaster. Tokens were leaking everywhere, and compliance was a nightmare. But I learned. These days, securing MCP servers isn't just about ticking boxes; it's about building a fortress. With tightening regulations and evolving threats, mastering workflows is crucial to make your MCP server robust and compliant. Let's dive into secure design principles, transitioning from local to remote servers, dynamic client registration, token management, and more. Trust me, grasping the more than ten enterprise-grade authorization specs makes all the difference.
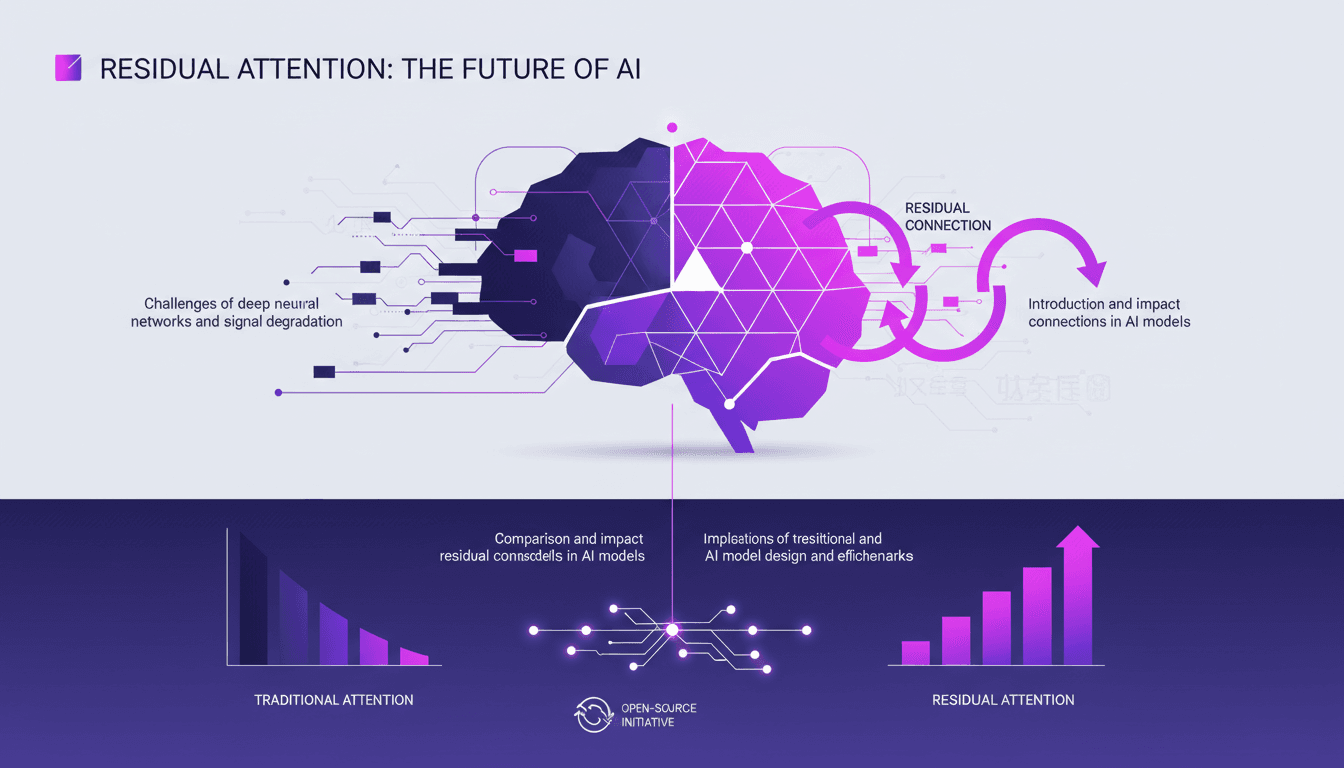
AI Breakthrough: Residual Attention Revolutionizes
I remember the first time I saw the impact of residual attention on AI models. It was like flipping a switch. Suddenly, inefficiencies that plagued deep learning for years were laid bare—and fixed. Since 2015, AI's foundations hadn't budged, but this breakthrough changes everything. Residual attention tackles signal degradation in deep neural networks, making models more efficient. Compared to traditional methods, it delivers superior performance on benchmarks. With open-sourcing, its potential impact is huge, notably in Chinese labs where hardware constraints drive innovation. But don't underestimate the complexity of integration.