Cross-App Access: Streamlining MCP with XAA
I've been deep in the trenches of enterprise developer platforms for almost 15 years, and trust me, managing Multi-Client Protocol (MCP) is no walk in the park. But there's a way to smooth things out: Cross-App Access (XAA). In this article, I dive into how I tackled these challenges head-on. MCP presents unique challenges, especially in complex enterprise environments. Leveraging identity providers like Octa, XAA simplifies managing cross-app access. We'll explore the implementation of XAA, the security implications of access tokens, and how CIMD and DCR standards compare. Get ready to rethink how you manage connections in enterprise environments.
I've been in the trenches of enterprise developer platforms for nearly 15 years, and let me tell you, managing Multi-Client Protocol (MCP) is no walk in the park. But there's a way to make it smoother: Cross-App Access (XAA). Have you ever found yourself spending time managing those dozens and dozens of consent screens for MCP servers? I have, and I got burned more times than I care to admit. By leveraging identity providers like Octa, XAA simplifies cross-app access management. In this talk, I'll share how I implemented XAA, tackling security implications of access tokens, and comparing CIMD and DCR standards head-on. I've learned the hard way that managing connections in enterprise environments requires a more thoughtful approach. Get ready to rethink your methods and anticipate the future with scoped access in XAA.
Understanding MCP and Its Challenges
Managing Multi-Client Protocol (MCP) is no walk in the park. Dealing with multiple client protocols across apps means juggling endless consent screens and dealing with token expiration. For us developers, it’s a headache, and for IT teams, it’s even worse. In enterprise environments, dozens and dozens of people are burning time managing these consent screens. And then there's the issue of tokens that remain active long after an employee leaves—an obvious security risk.
Cross-App Access (XAA) as a Solution
So, how do we tackle this? With Cross-App Access (XAA). This system streamlines access management across multiple apps. Thanks to identity providers like Octa, we can breathe easier. XAA reduces managerial overhead and enhances security by mitigating token expiration risks. Less manual oversight, more security, and a much smoother user experience overall.

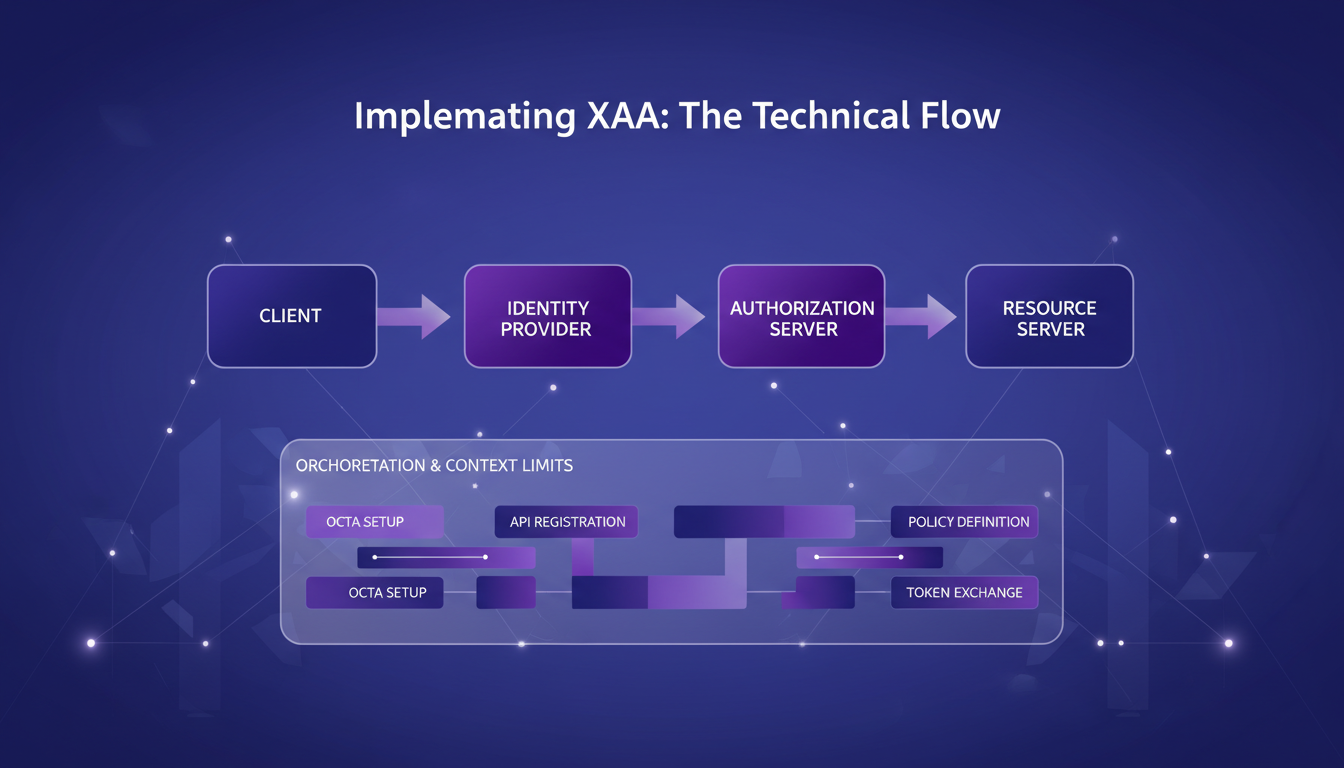
Implementing XAA: The Technical Flow
So, how does XAA actually work? We’ve got four key systems: the client, the identity provider (Octa), the authorization server (Figma), and the resource server (Figma API). It might sound technical, but once you get it, it makes life easier. You set up connections between apps in the manage connections portal. Pay attention to token usage and expiration settings—they’re crucial to avoid nasty surprises.
Security Implications and Solutions
Access tokens can be a real risk if not managed properly. Typically, they expire after five minutes, but you’ve got to keep an eye on them. Solutions include regular token rotation and scoped access. It's crucial to always plan for improvements to strengthen security within XAA. Essentially, our systems need to be orchestrated to remain secure.
Comparing CIMD and DCR Standards
Now, let’s talk standards. CIMD and DCR are two standards for managing MCP. CIMD is newer but sometimes lacks ecosystem support. DCR, being older, is well-established but can be less modern. So, the choice really hinges on your specific needs. In enterprise settings, the standard choice depends on technical constraints and security objectives.
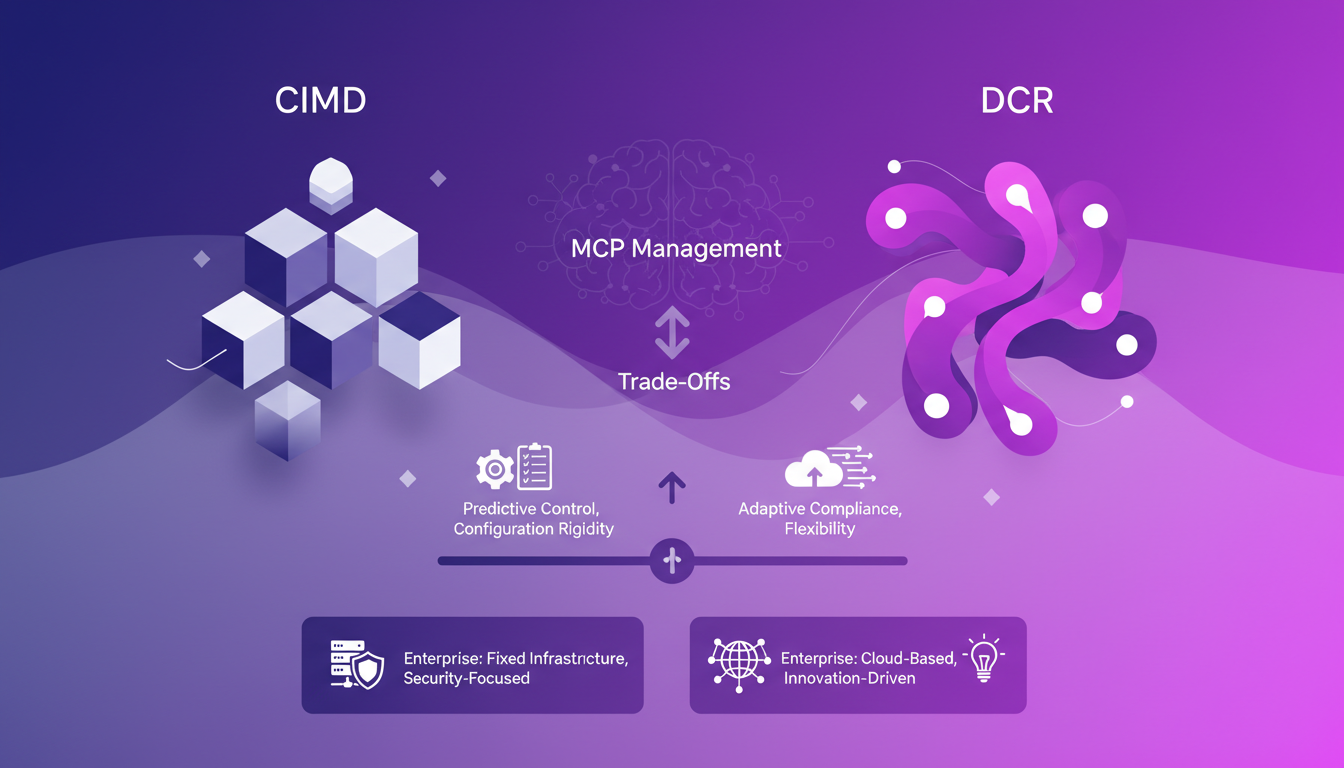
Every choice comes with its pros and cons, and there is no one-size-fits-all solution. But by fully understanding each one’s limits and benefits, you can better decide which to adopt.
I've dived into implementing XAA, and honestly, it's been a game changer for managing cross-app access. With four systems involved (client, identity provider like Octa, resource authorization server, and the API), understanding the technical flows and standards like CIMD and DCR is crucial. Here's what really made a difference:
- Streamlined Operations: By integrating XAA, I've cut down the time dozens of team members spend on consent screens.
- Enhanced Security: The security implications are significant; it's more robust.
- Interoperability: With Octa, identity management flows smoothly across apps.
I'm convinced that for anyone managing complex MCPs, XAA can be the key to simplifying and securing your workflows. Ready to simplify your MCP management with XAA? Start by evaluating your current setup to identify where XAA can make the most impact. And for a deeper dive, check out Garrett Galow's video "One Login to Rule Them All". It will give you practical insights you won't find elsewhere.
Frequently Asked Questions

Thibault Le Balier
Co-fondateur & CTO
Coming from the tech startup ecosystem, Thibault has developed expertise in AI solution architecture that he now puts at the service of large companies (Atos, BNP Paribas, beta.gouv). He works on two axes: mastering AI deployments (local LLMs, MCP security) and optimizing inference costs (offloading, compression, token management).
Related Articles
Discover more articles on similar topics
GPT 5.5: Token Speed and Enterprise Strategy
I dove into GPT 5.5 the moment it dropped, and let me tell you, the 20% token speed boost isn't just a number—it's a game changer for real-time applications. But there's more under the hood than just speed. Released on April 23, 2026, this model marks a rapid evolution in OpenAI's offerings. This isn't just about new features; it's a strategic pivot towards enterprise solutions, optimizing infrastructure, and redefining efficiency. We'll explore the release of GPT 5.5, Entropique's market strategy, the impact of Cloud Code on the coding landscape, and how OpenAI is reshaping its approach to conquer the enterprise markets.
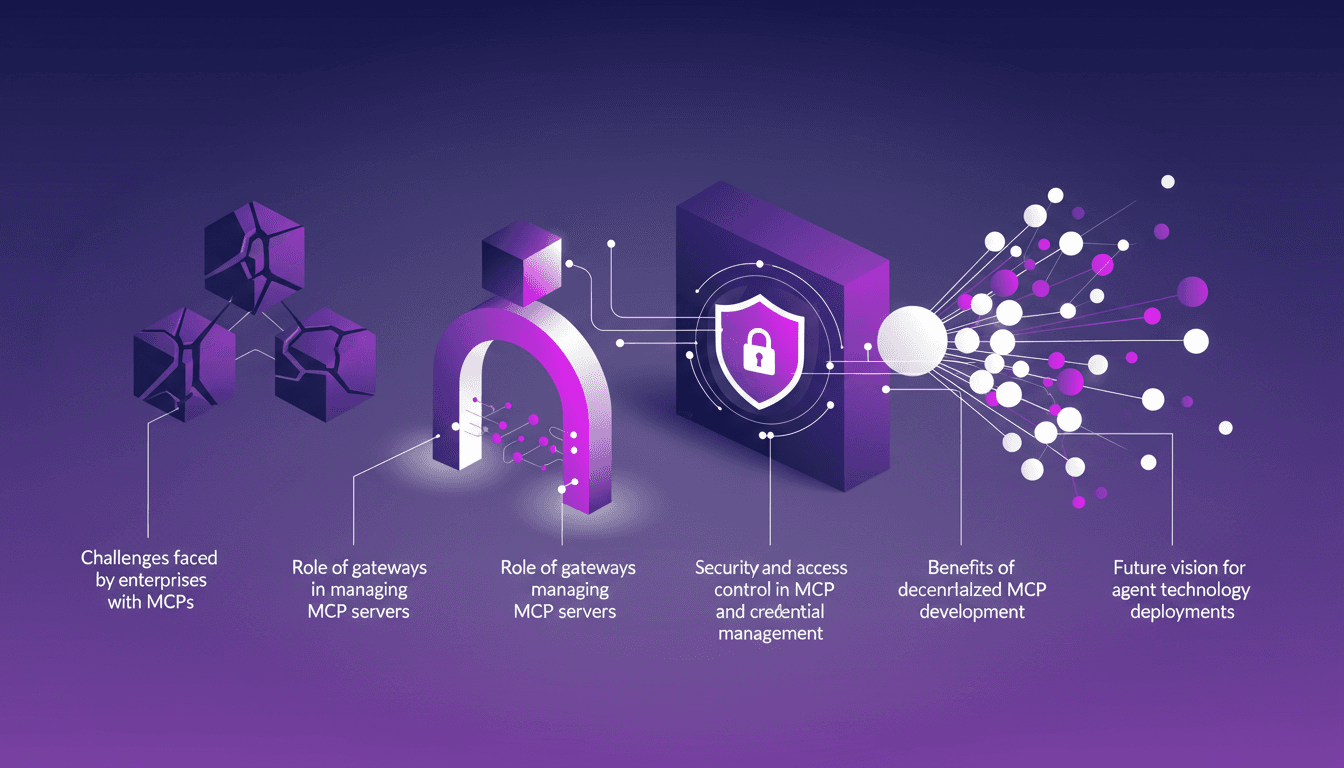
Enterprise MCP Challenges: Practical Solutions
I remember the first time I had to scale MCP servers for an enterprise client. It was utter chaos — but once I found the right orchestration, everything clicked. Enterprises face unique challenges with MCPs, from scalability to security. In this article, let's break down how to tackle these challenges using gateways and other strategies. We'll also dive into security and access control, the importance of observability and credential management, and not to forget the future vision for agent technology deployment.
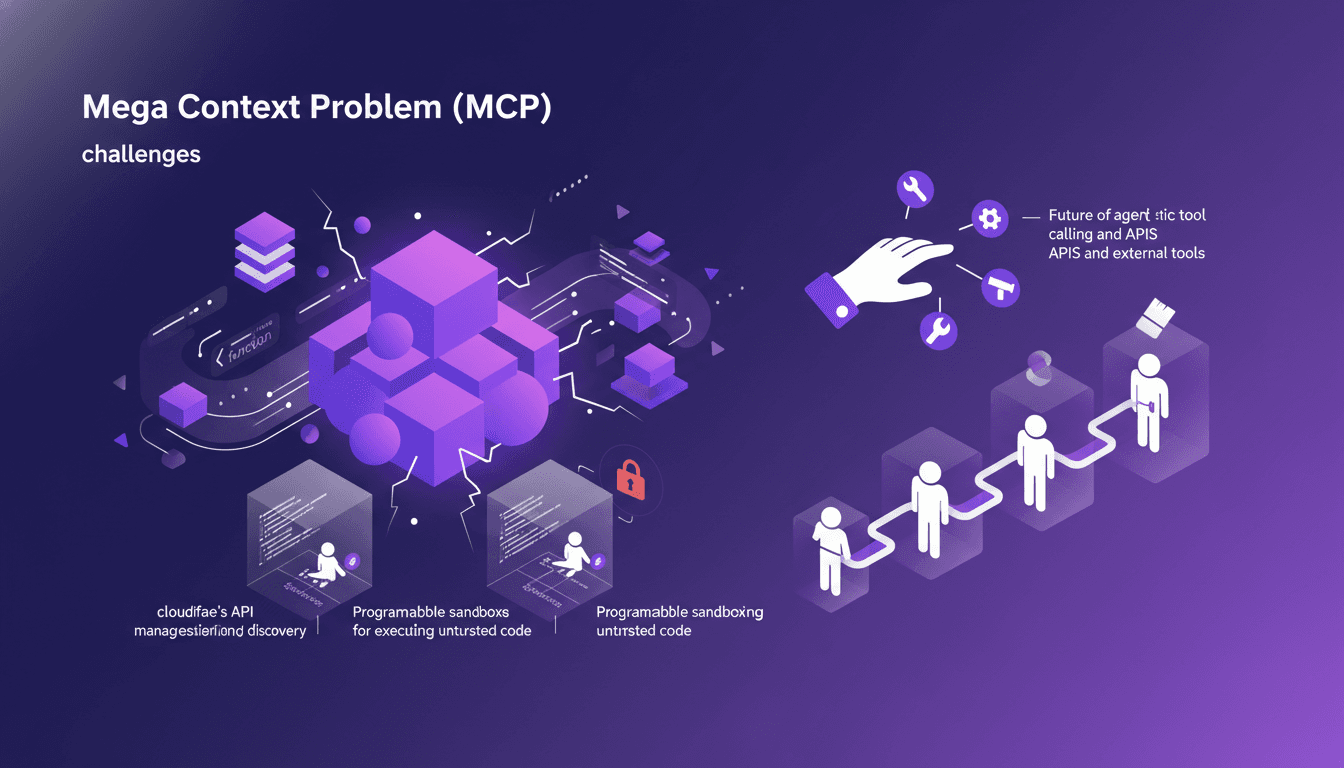
Tackling MCP: Managing Context with Cloudflare
I remember the first time I hit the Mega Context Problem (MCP) head-on. I was knee-deep in API calls, and my context window was overflowing. That's when I realized managing context isn't just a technical challenge; it's a strategic one. With tools like Cloudflare's API management and TypeScript, we can tackle this beast head-on. I dive into these tumultuous waters daily, and I'll share the lessons I've learned. We'll discuss MCP challenges, the evolution of MCP clients, and the implications of programmatic tool calling. It's not just about technology but strategic orchestration.
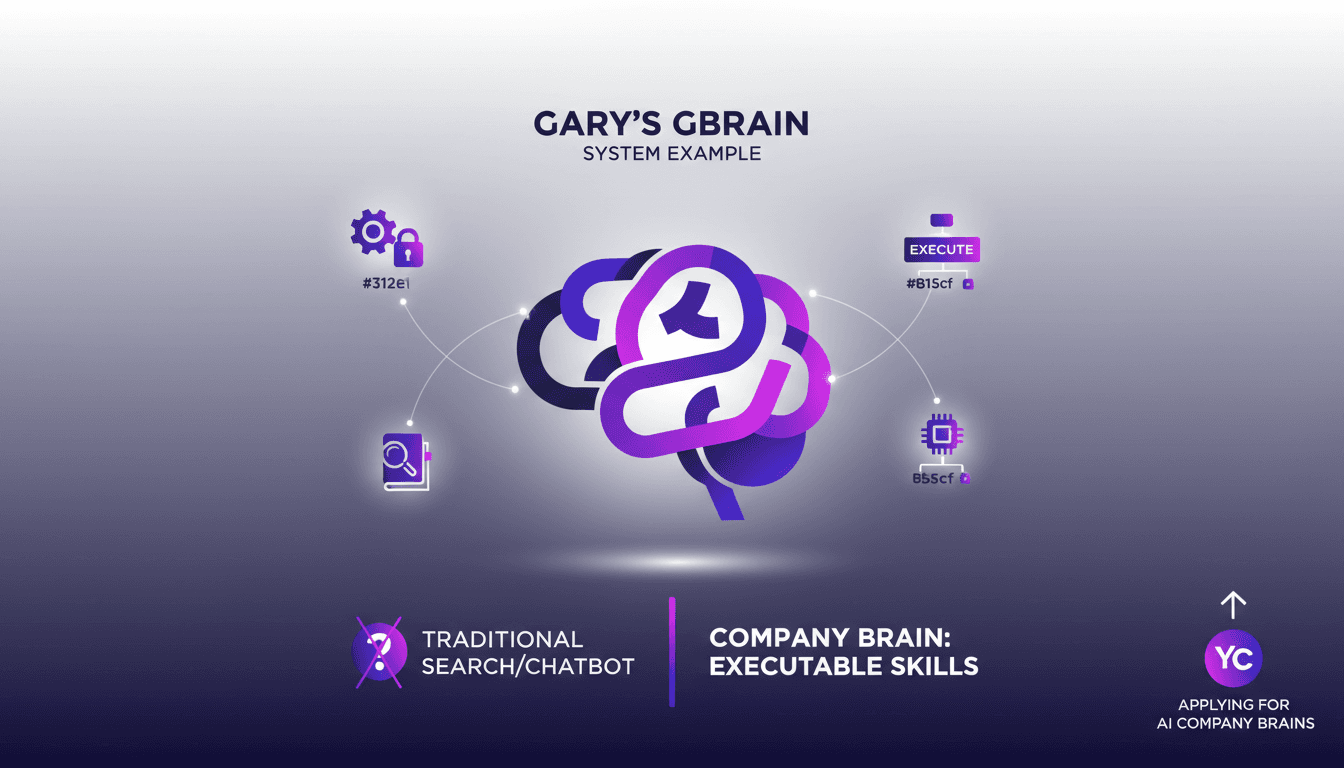
AI Automation: Challenges and Practical Solutions
I vividly remember my first attempt at implementing AI automation in my company—what a mess! But once I grasped the importance of domain knowledge and the 'company brain' concept, things started to make sense. In this article, I share how I tackled these challenges using Gary's GBrain as an example. Too often, companies hit a wall with AI because they overlook the real key: domain knowledge. I'll walk you through how I built a company brain and why every business should have one today.
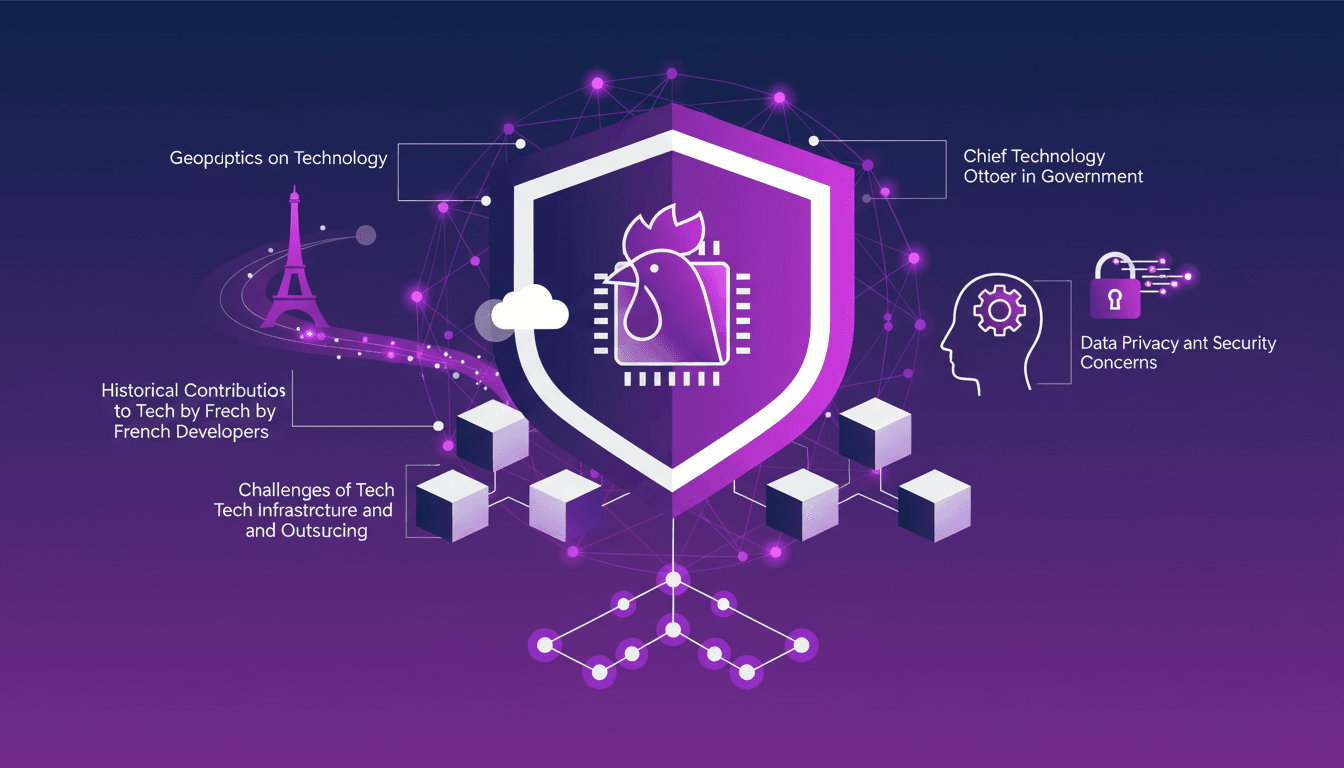
Tech Sovereignty: Rebuilding France's Stack
I remember the moment I realized tech sovereignty wasn't just a buzzword. It was when I tried to navigate the maze of outsourced infrastructure and felt the limitations firsthand. France, with its rich history in tech, needs to reclaim its stack. In an age where technology dictates geopolitical power, France stands at a crossroads. With historical contributions to tech and a pressing need for resilient infrastructure, it's time to explore the role of leadership and the future of a decentralized, secure web. Let's dive into why and how we rebuild our stack.